Vaultless Tokenization and Its Role in PCI DSS Compliance
In an era where data breaches and cyber threats are on the rise, safeguarding sensitive information […]

7 cutting-edge encryption techniques for reimagining data security
Secret codes have been around for hundreds of years. Everyone from pirates to diplomats have used […]

Die 10 häufigsten IT-Sicherheitsfehler
srcset=”https://b2b-contenthub.com/wp-content/uploads/2025/03/shutterstock_2491155871.jpg?quality=50&strip=all 12500w, https://b2b-contenthub.com/wp-content/uploads/2025/03/shutterstock_2491155871.jpg?resize=300%2C200&quality=50&strip=all 300w, https://b2b-contenthub.com/wp-content/uploads/2025/03/shutterstock_2491155871.jpg?resize=768%2C512&quality=50&strip=all 768w, https://b2b-contenthub.com/wp-content/uploads/2025/03/shutterstock_2491155871.jpg?resize=1024%2C683&quality=50&strip=all 1024w, https://b2b-contenthub.com/wp-content/uploads/2025/03/shutterstock_2491155871.jpg?resize=1536%2C1024&quality=50&strip=all 1536w, https://b2b-contenthub.com/wp-content/uploads/2025/03/shutterstock_2491155871.jpg?resize=2048%2C1365&quality=50&strip=all 2048w, https://b2b-contenthub.com/wp-content/uploads/2025/03/shutterstock_2491155871.jpg?resize=1240%2C826&quality=50&strip=all 1240w, https://b2b-contenthub.com/wp-content/uploads/2025/03/shutterstock_2491155871.jpg?resize=150%2C100&quality=50&strip=all 150w, […]
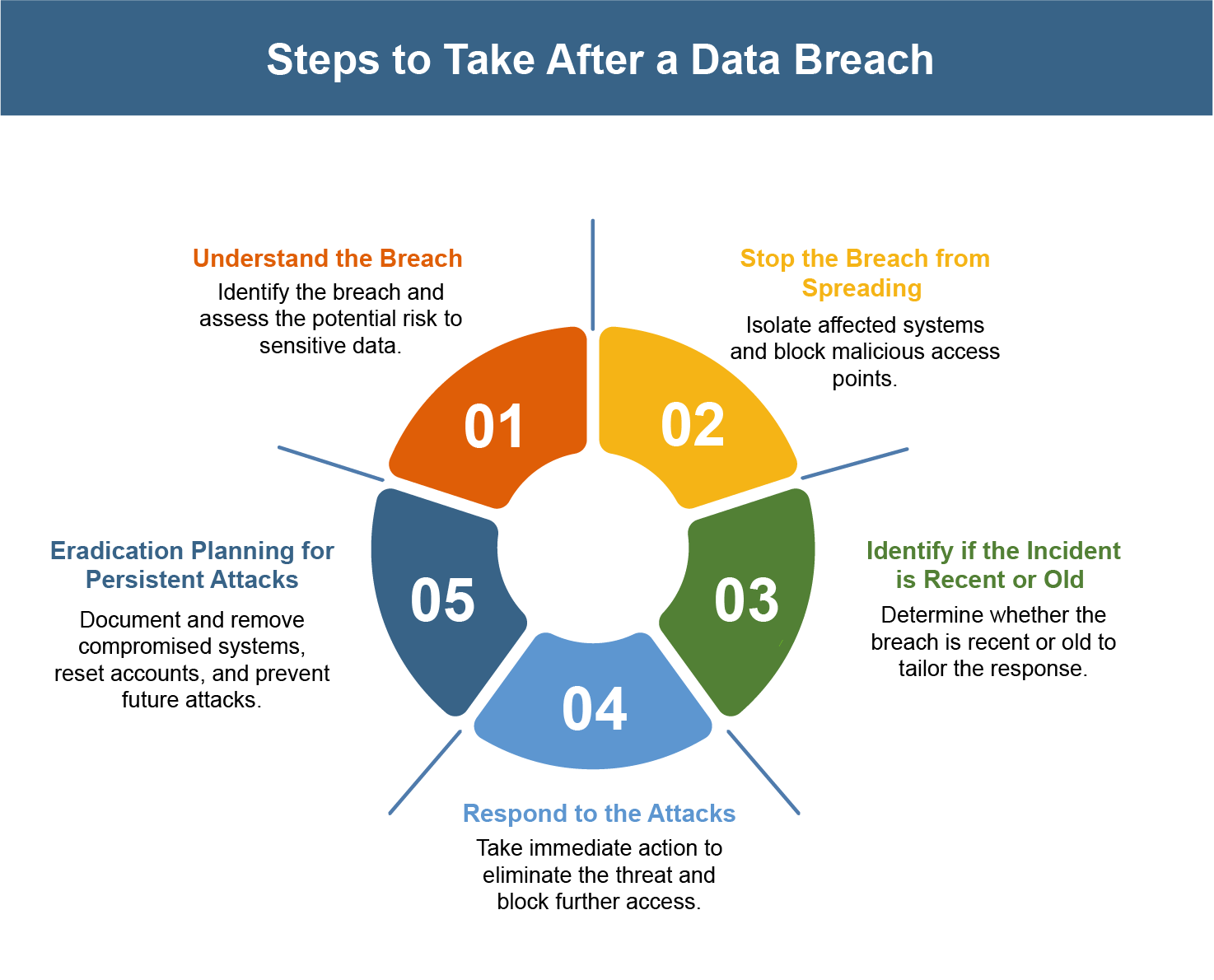
What Should a Company Do After a Data Breach? The First 5 Steps to Take
Cyberattacks and data breaches can’t be completely stopped in a day. As technology grows, attackers find […]

Even anti-scammers get scammed: security expert Troy Hunt pwned by phishing email
Troy Hunt, the security researcher behind the popular “Have I Been Pwned?” data breach notification site […]

KI-Agenten erobern die Cybersicherheitsbranche
Microsoft führt KI-Agenten ein, um die Cybersicherheit angesichts zunehmender Bedrohungen zu automatisieren. Denis Linine – shutterstock.com […]

Mit GenAI zum Insider-Threat
Viele Unternehmen haben nicht auf dem Schirm, welche Sicherheitsprobleme durch die Nutzung von GenAI entstehen. Teerachai […]

The Role of Sandbox Analysis in advanced Malware Detection
Malware continues to evolve with greater sophistication. Sandbox malware analysis offers a secure testing ground to […]

VMware plugs a high-risk vulnerability affecting its Windows-based virtualization
Broadcom is warning customers of a high-severity, authentication bypass flaw, now fixed, affecting VMWare Tools for […]

Legal impact on cybersecurity in 2025: new developments and challenges in the EU
In the fast-paced world of cybersecurity, 2025 is shaping up to be a crucial year for […]
