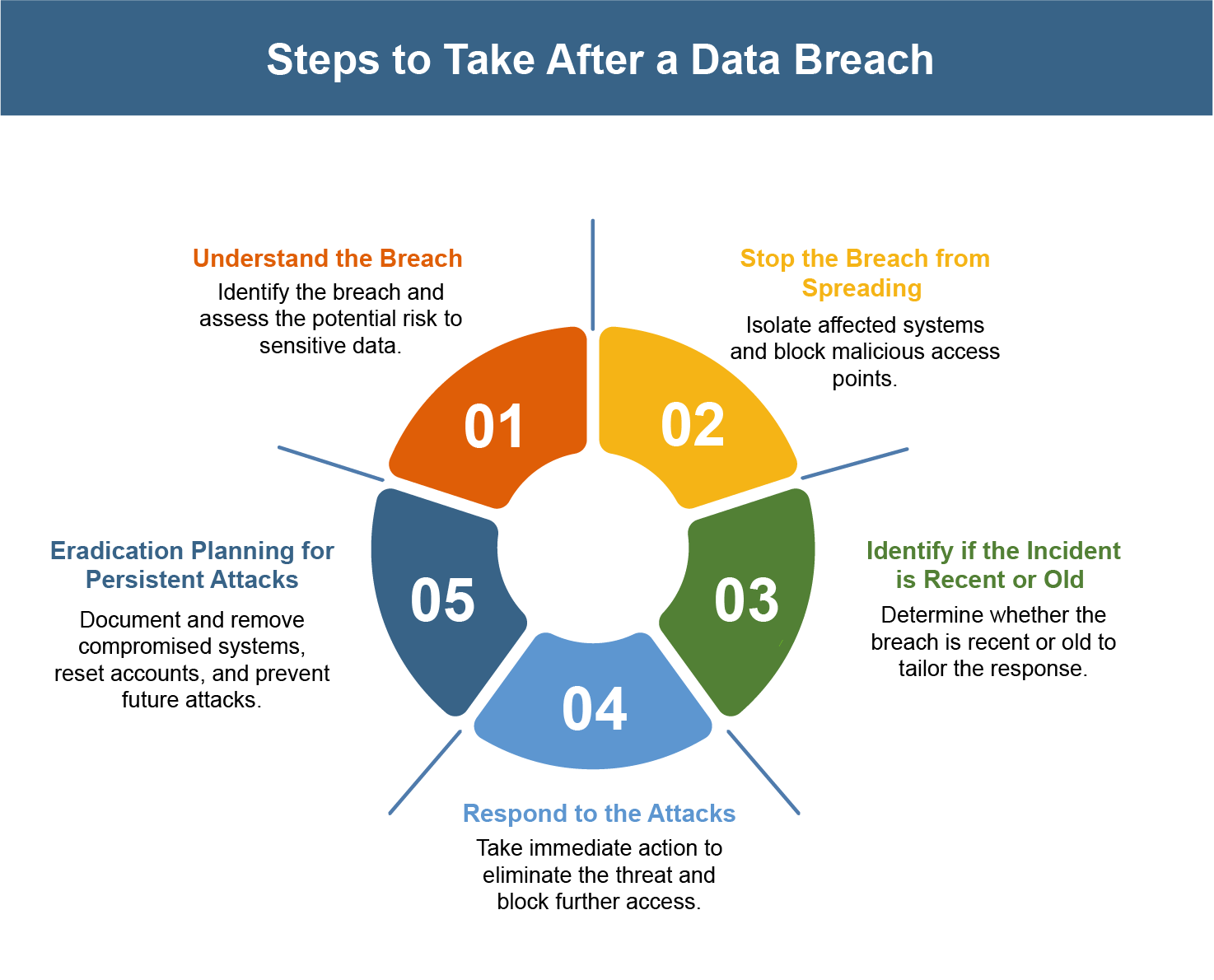
What Should a Company Do After a Data Breach? The First 5 Steps to Take
Cyberattacks and data breaches can’t be completely stopped in a day. As technology grows, attackers find […]

Even anti-scammers get scammed: security expert Troy Hunt pwned by phishing email
Troy Hunt, the security researcher behind the popular “Have I Been Pwned?” data breach notification site […]

KI-Agenten erobern die Cybersicherheitsbranche
Microsoft führt KI-Agenten ein, um die Cybersicherheit angesichts zunehmender Bedrohungen zu automatisieren. Denis Linine – shutterstock.com […]

Mit GenAI zum Insider-Threat
Viele Unternehmen haben nicht auf dem Schirm, welche Sicherheitsprobleme durch die Nutzung von GenAI entstehen. Teerachai […]

The Role of Sandbox Analysis in advanced Malware Detection
Malware continues to evolve with greater sophistication. Sandbox malware analysis offers a secure testing ground to […]

VMware plugs a high-risk vulnerability affecting its Windows-based virtualization
Broadcom is warning customers of a high-severity, authentication bypass flaw, now fixed, affecting VMWare Tools for […]

Legal impact on cybersecurity in 2025: new developments and challenges in the EU
In the fast-paced world of cybersecurity, 2025 is shaping up to be a crucial year for […]

Rising attack exposure, threat sophistication spur interest in detection engineering
Detection engineering, which was once a niche practice among mostly large companies, appears to have evolved […]

Critical RCE flaws put Kubernetes clusters at risk of takeover
The Kubernetes project has released patches for five vulnerabilities in a widely used popular component called […]