This AI Agent Is Quietly Leaving OpenClaw in the Dust
Quick vibes check: a 78-year-old marketing exec who had never written code shipped a working robotics […]
OpenAI Opens Cyber Model to EU While Anthropic Keeps Mythos Restricted
OpenAI’s newest cybersecurity model is landing in Europe as the country pushes for access to the […]
Bots Now Outnumber Humans Online as Chrome Becomes Their Top Disguise
The internet is now more machine than human. Bots accounted for 53% of observed web traffic […]
Vibe Coding Cheat Sheet: Tools, Prompts, Security Tips, and More
Software development is undergoing a seismic shift as vibe coding turns plain English into functional applications […]
Thousands of AI ‘Vibe Coding’ Apps May Expose Sensitive Medical, Business Data
The promise of building apps with a few text prompts is turning into a growing cybersecurity […]
Google Chrome Reportedly Installs 4GB AI Model Without Clear Opt-In
Your browser may have downloaded an AI model behind your back… and you might never know. […]
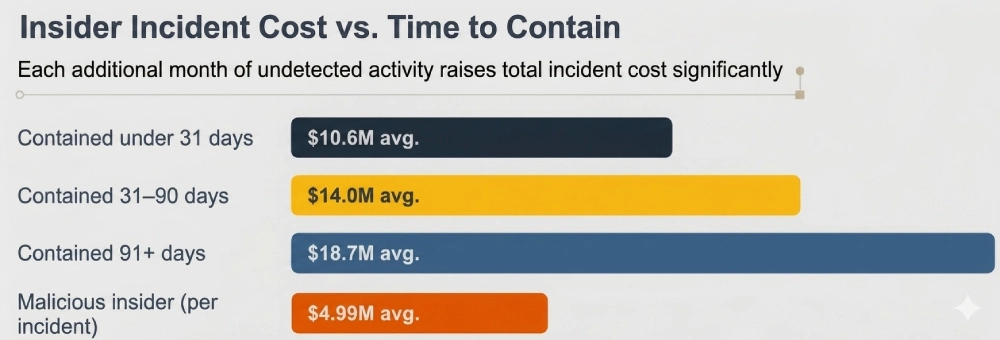
What Insider Threat Monitoring Reveals About Hidden Organizational Risk
Key Takeaways Insider monitoring exposes gaps between policy and real data behavior Overprivileged access remains one […]
Trump Eyes Federal Reviews for Advanced AI Models Before Launch
Washington may be getting nervous about what the next frontier AI model can do before the […]
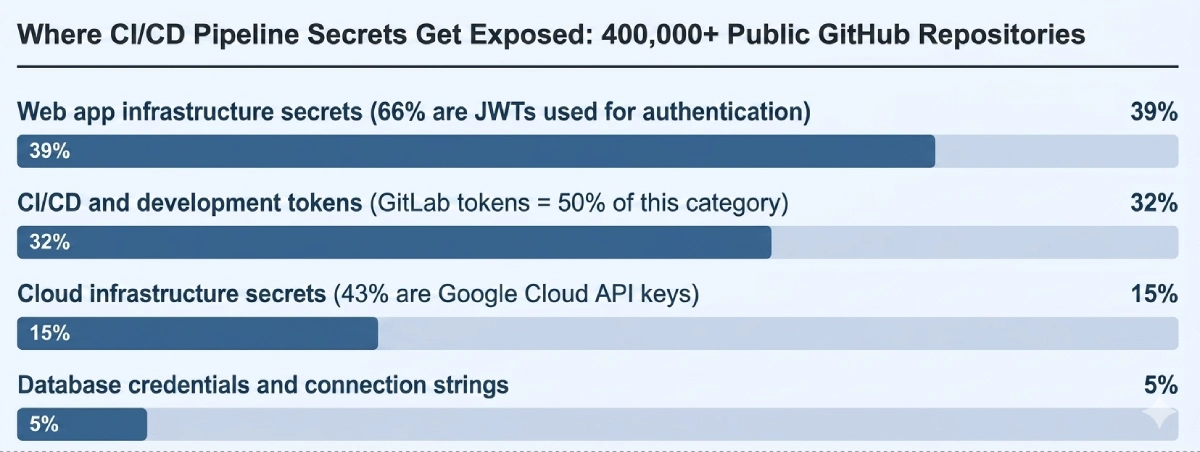
CI/CD Pipeline Security Tools and Technologies
Key Takeaways CI/CD security requires stage-specific tools; no single platform covers the full pipeline risk surface. […]
‘Patch Wave’ Warning: AI May Expose Decades of Hidden Software Bugs
The UK’s National Cyber Security Centre issued an unusual warning about what’s coming next. AI, the […]