SSH DDoS Attack Simulation Using Python: A Comprehensive Guide
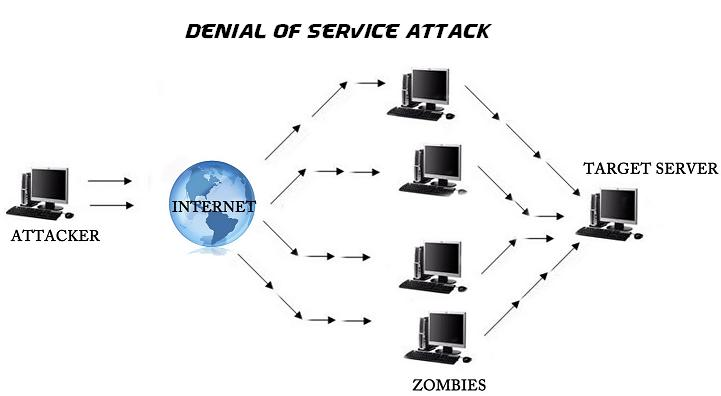
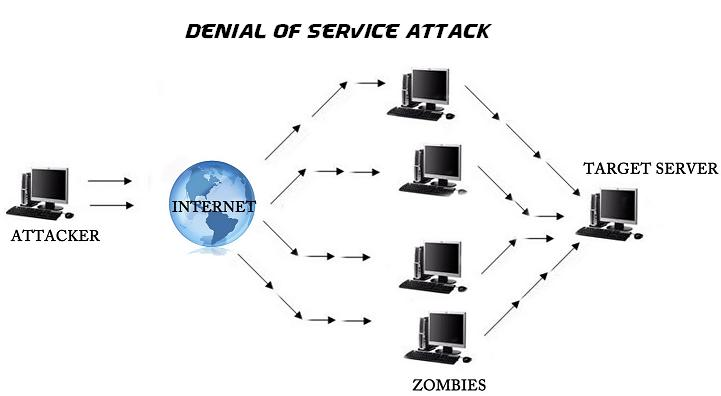
Hey guys! 👋 Rocky here. Let’s talk about something wild but super important: DDoS attacks targeting […]
SSH DDoS Attack Simulation Using Python: A Comprehensive Guide
Hey guys! Rocky here. Let’s talk about something wild but super important: DDoS attacks targeting SSH—and […]
The Ultimate Guide to Transforming Your Old Machine into a VPS Server
Hey guys, Rocky here! 👋 So you’ve got a dusty old laptop or computer taking up […]
The Ultimate Guide to Transforming Your Old Machine into a VPS Server
Hey guys, Rocky here! 👋 So you’ve got a dusty old laptop or computer taking up […]
The Ultimate Guide to Transforming Your Old Machine into a VPS Server
Hey guys, Rocky here! So you’ve got a dusty old laptop or computer taking up space […]

Building Malware with Python: Writing Ransomware, Keyloggers & Reverse Shells from Scratch
Hey guys, Rocky here! 👋 So you’re curious how malware actually works? Maybe you’re wondering why […]

Building Malware with Python: Writing Ransomware, Keyloggers & Reverse Shells from Scratch
Hey guys, Rocky here! 👋 So you’re curious how malware actually works? Maybe you’re wondering why […]

Building Malware with Python: Writing Ransomware, Keyloggers & Reverse Shells from Scratch
Hey guys, Rocky here! So you’re curious how malware actually works? Maybe you’re wondering why ransomware […]
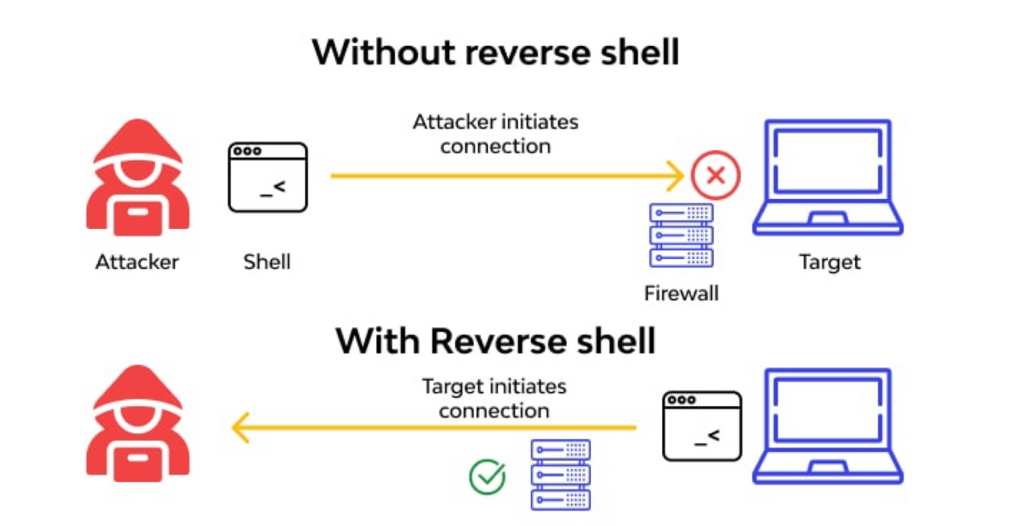
Building a Custom Python Backdoor
Hey guys! 👋 Rocky here. So, you wanna learn how to build a custom backdoor in […]
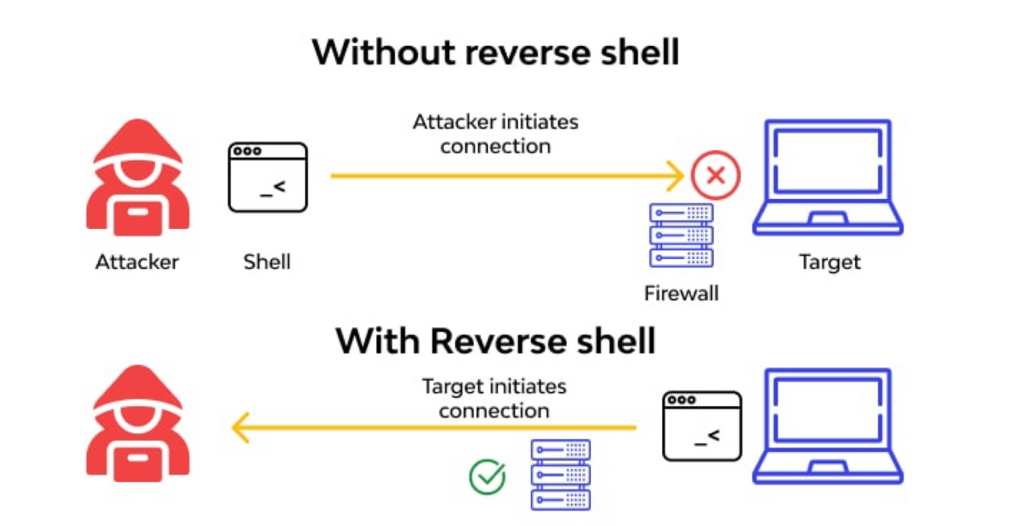
Building a Custom Python Backdoor
Hey guys! 👋 Rocky here. So, you wanna learn how to build a custom backdoor in […]