
CISOs: Align cyber risk communication with boardroom psychology
By now, executive boards across industries understand that cyberattacks can be costly. What they often lack, […]

Ten years later, has the GDPR fulfilled its purpose?
This year marks the 10th anniversary of the EU’s adoption of the General Data Protection Regulation, which […]

US government agency to safety test frontier AI models before release
The Center for AI Standards and Innovation (CAISI), a division of the US Department of Commerce, […]
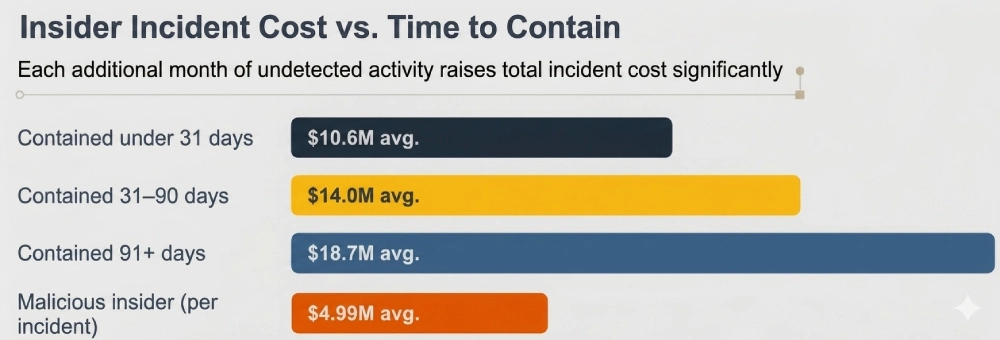
What Insider Threat Monitoring Reveals About Hidden Organizational Risk
Key Takeaways Insider monitoring exposes gaps between policy and real data behavior Overprivileged access remains one […]

Iranian state-backed spies pose as ransomware slingers in false flag attacks
An Iranian state-sponsored espionage group is pretending to be a regular ransomware gang in a new […]

New malware turns Linux systems into P2P attack networks
Attackers have found a new way to turn Linux systems into stealthy supply chain distribution hubs […]
The CISO’s DPDP Framework: Security Controls to Board-Level Accountability
The Digital Personal Data Protection (DPDP) Act of India is a decisive move in the direction […]

Poisoned truth: The quiet security threat inside enterprise AI
As enterprises rush to deploy internal LLMs, AI copilots, and autonomous agents, most security conversations focus […]

Train like you fight: Why cyber operations teams need no-notice drills
St. Michael’s Hospital in Toronto recently executed a full Code Orange simulation: A mass casualty emergency […]

Die besten DAST- & SAST-Tools
Tools für Dynamic und Static Application Security Testing helfen Entwicklern, ihren Quellcode zu härten. Wir zeigen […]
