Key Takeaways
Insider monitoring exposes gaps between policy and real data behavior
Overprivileged access remains one of the most common hidden risks
Shadow data increases breach cost by 16.2% and delays containment
Behavioral signals often appear weeks before an incident occurs
55% of insider threats stem from negligence, not malicious intent
Detection alone isn’t enough, real-time DLP enforcement is critical
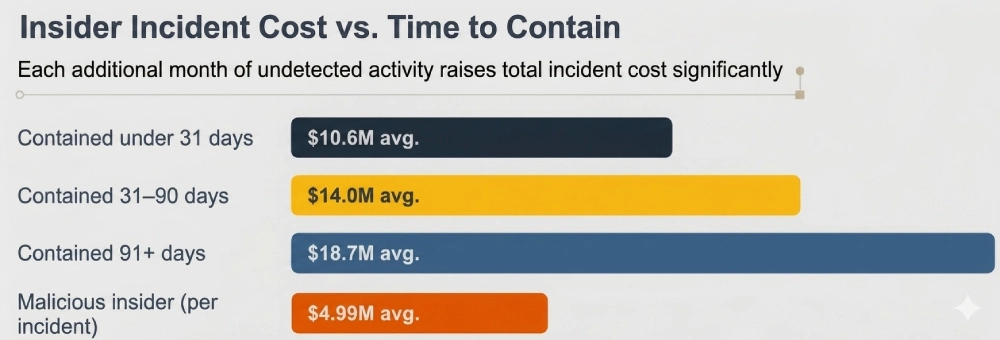
Faster detection directly reduces breach costs by millions
Security teams that deploy insider threat monitoring for the first time rarely catch what they went looking for. They wanted a bad actor. What they found was a ground-truth map of how their organization actually handles sensitive data, and in most cases, that map looked nothing like the policies on paper.
That gap, between documented security controls and real-world data behavior, is precisely what insider threat monitoring exposes. Across organizations that have gone through this process, the hidden risks it surfaces follow consistent, predictable patterns.
This article breaks down what those patterns are, what the research says about their financial consequences, and what a detection program must be capable of to actually close the exposure window.
What Does Insider Threat Monitoring Actually Reveal?
The title question deserves a direct answer first. When comprehensive insider threat monitoring is deployed with full network and user activity visibility, four findings consistently appear across organizations, regardless of industry, size, or existing security maturity.
Access rights that were never scoped or revoked. Privileged users routinely carry access to sensitive systems tied to projects from years ago. Nobody removed it. Nobody reviewed it. Monitoring makes this visible at workforce scale, not just in the handful of accounts IT happened to audit manually last quarter.
Sensitive data moving through channels that nobody was watching. Encrypted traffic on non-standard ports. Compressed files attached to personal emails. Syncs to consumer cloud storage apps running quietly in the background during business hours. These aren’t edge cases; they show up in most environments within the first week of deploying network-level visibility, because nobody was looking before.
Shadow data in locations nobody knew about. Customer records, financial models, source code sitting in unmanaged file shares, personal drives, or SaaS tools outside IT governance. The IBM Cost of a Data Breach Report 20241 found that more than one-third of all breaches involved shadow data. These incidents cost 16.2% more on average while taking 26% longer to contain.
Behavioral patterns that precede incidents by weeks. An employee under a performance review downloading bulk records outside their normal scope. A contractor accessing systems irrelevant to their current engagement. An account pulling from file servers in a timezone where no staff member is based, at 2 a.m. Individually, each of these can look routine. Tracked across a behavioral timeline, they’re exactly what post-incident forensic investigators reconstruct, except monitoring surfaces them before the damage is done.
That is the complete answer. Insider threat monitoring does not just find threats. It finds the structural vulnerabilities: overprivileged access, untracked data movement, shadow data, and early-stage behavioral indicators. These are the factors that transform routine employee actions into organizational risk.
The Real Scale of Insider Risk in 2026
The numbers from 2025 and 2026 research make clear that insider threat risk isn’t declining. It’s getting more expensive, more frequent, and in most organizations, still significantly underfunded compared to perimeter defenses.
$19.5M
Avg. annual cost of insider incidents per organization
76%
Of organizations reported insider attacks in the past year
81 days
Average time to contain an insider incident
60%
Of confirmed breaches involve a human element
The 2026 Ponemon Cost of Insider Risks Global Report2 put the average annual cost of insider security incidents at $19.5 million per organization, the highest figure the report has recorded since its inception. In North America specifically, that cost now stands at $22.2 million annually per organization, up from $11.1 million in 2018. That’s a doubling in six years, and nothing in the trend data suggests it’s slowing.
The 2025 Verizon DBIR3, drawn from 22,052 incidents and 12,195 confirmed breaches across 139 countries, found the human element present in roughly 60% of all breaches. That figure hasn’t changed much across reporting cycles. Which is itself the problem: the human layer is consistently the most exposed and the least directly addressed.
6 Hidden Risk Signals That Insider Threat Monitoring Surfaces
These are not hypothetical attack vectors. They’re the patterns that security teams regularly find when deploying comprehensive monitoring for the first time, often in environments they believed were already well-secured.
Hybrid Infrastructure, Hidden Risk: The Visibility Problem CISOs Must Address
Practical Playbook for Improving Visibility Across Hybrid Infrastructure:
Prioritizing Visibility That Supports Incident ResponseOperationalizing Visibility Through Continuous ValidationCentralizing Telemetry Without Centralizing InfrastructureRead the Whitepaper
What Monitoring Finds in Most Organizations
Common findings when insider threat detection is deployed with full network and user activity visibility
Abnormal Data Movement
Bulk transfers to personal email addresses, consumer cloud storage, or removable media, often outside working hours or far beyond what a user’s role requires
Privilege Creep
Access rights that accumulated over years and were never revoked, leaving users with system access well beyond their current job function.
Non-Standard Protocol Use
Data routed through obscure ports or protocols that fall outside standard monitoring coverage. This is a known method for avoiding detection.
Shadow Data Exposure
Sensitive customer records, IP, or financial data sitting in personal drives, unapproved SaaS tools, or file shares that aren’t under active security governance.
Off-Hours Access Spikes
Sharp increases in data retrieval or system access at unusual times. This is a consistent early indicator of either pre-departure exfiltration or compromised account activity.
Unauthorized Data Snooping
Repeated access to records or systems outside a user’s documented role, with no corresponding business justification on file.
Why Insider Threats Are So Hard to Detect
In 2024, 90% of security professionals said insider attacks are as difficult or more difficult to detect than external ones, up from just 50% holding that view five years earlier, per the Cybersecurity Insiders 2024 Insider Threat Report4. That shift reflects a real and growing problem.
External attackers have to force their way in. Insiders are already inside. They’re using credentials the system recognizes. Accessing systems they’re authorized to use. Moving data through channels the organization built. There’s no attack signature to match against. No perimeter anomaly to trigger an alert. The only signal is behavioral, and you only catch it if you’re continuously watching behavior.
The same report identified the three structural conditions making insider threat detection harder each year: the expanding attack surface created by cloud and SaaS adoption, growing infrastructure complexity from hybrid and remote work environments, and the absence of consistent data classification policies. These aren’t technical bugs. They’re organizational conditions that create persistent blind spots, and they don’t get fixed without monitoring that’s designed to address them directly.
Negligence vs. Malicious Intent: What the Data Actually Shows
Most insider threat programs are designed around the malicious insider scenario, the employee who deliberately steals intellectual property or sabotages critical systems on their way out the door. That scenario is real, but the research shows it is the wrong place to concentrate most attention.
The Ponemon Institute’s 20252 findings showed that 55% of insider incidents stem from employee negligence, at a total annual cost of $8.8 million per organization. Malicious insiders drive 25% of incidents, averaging $715,366 each. Credential theft accounts for the remaining 20%, at $779,707 per incident and the highest cost per event of the three categories.
“Organizations spend $211,021 per incident on containment and just $37,756 on monitoring. Early detection isn’t a security expense; it’s a cost reduction strategy.”
Negligence doesn’t usually look alarming in the moment. An employee emails a sensitive contract to their personal account because they want to review it at home. A contractor uploads a proposal document to Google Drive because the approved tool keeps timing out. A manager forwards a customer list to a colleague who asked for it informally. None of these feel like security incidents to the people involved. But each one represents the unauthorized movement of sensitive data, and with real-time network enforcement, each one can be blocked in transit before the data arrives at its destination.
Detection that only generates an alert doesn’t solve the negligence problem. The transfer is already complete by the time an analyst reviews it. The value of automated, policy-enforced blocking at the network layer is specifically that it interrupts negligent behavior at the moment it occurs, not hours or days later.
Data Exfiltration Paths That Most Organizations Miss
Programs that monitor only email attachments and USB activity leave significant gaps. Insiders, and external attackers using compromised credentials, know which channels are watched. They use the ones that are not.
The IBM 2024 breach report found intellectual property theft increased 27% year-over-year, with the cost per compromised IP record climbing to $173. Breaches involving data spread across multiple environments averaged more than $5 million in total cost and took 283 days to identify and contain. This is nearly three times the timeline of single-environment incidents. That extended window exists because multi-environment data movement is harder to track, not because the attacks are more sophisticated.
The exfiltration channels monitoring catches most often, but that organizations least expect, include encrypted traffic on non-standard ports, data embedded inside compressed archives, transfers staged through background cloud-sync clients, and content moved to external contacts through collaboration tools. Every one of these requires session-level inspection to surface, because the content is not readable at the packet layer.
How Behavioral Analytics Improve Insider Threat Detection
Static access policies define what’s permitted. Behavioral analytics identify what’s unusual. That distinction is what closes the gap between authorized access and harmful use of that access.
A sales engineer downloading customer records is probably just doing their job. That same engineer pulling records across five product lines during the final week before their resignation notice is a completely different signal. The first event is routine. The second is a risk indicator. The difference is only visible through behavioral baselines built from actual historical activity, not rules written into a policy document months earlier.
User and entity behavior analytics (UEBA) build those baselines from real data: which systems a user typically accesses, what hours they work, how much data they move in a given period, and which colleagues they regularly interact with. Deviations from baseline, especially when they span multiple systems, occur in combination, or appear alongside other anomalies, are what surface potential insider threat incidents before they escalate into confirmed breaches.
The Ponemon 2025 report found 51% of organizations now consider AI and machine learning essential or very important in detecting and preventing insider risks. The top three benefits their teams reported: reduced investigation times (70%), improved behavioral insights (59%), and lower required skill level for analysts (58%). Automation doesn’t replace analyst judgment. It focuses analyst attention on the signals that actually warrant it, instead of every low-confidence alert in a noisy queue.
From Ponemon 2025: Organizations with a formal insider risk management program were 65% more likely to pre-empt a data breach through early detection. The report describes it as the only security strategy studied that enabled proactive breach prevention rather than reactive response.
Why Privileged Users Carry the Highest Insider Threat Risk
Insider risk isn’t evenly distributed across a workforce. Privileged users, those with administrative or elevated system access, carry disproportionate risk because their authorized reach covers a far broader set of critical assets and sensitive data than any standard employee ever touches.
Concern about malicious privileged insiders among security professionals rose from 60% in 2019 to 74% in 2024, according to Cybersecurity Insiders. The SIFMA 2024 Insider Threat Best Practices Guide5 documents specific cases in financial services where privileged users leveraged elevated credentials to embezzle funds and exfiltrate account data for hundreds of thousands of clients. The common thread across every documented case: the access was legitimate. The behavior wasn’t.
Monitoring programs that apply the same behavioral thresholds to privileged and standard users undercount the actual risk concentration in the access tiers that matter most. A more effective approach applies tighter behavioral baselines, more frequent access reviews, and session-level recording specifically to high-privilege roles, because the potential damage from a single compromised or malicious privileged account is categorically different from a standard employee event.
How Network DLP Stops Data Exfiltration From Insider Threats
Behavioral analytics surface the intent signals. Network data loss prevention stops the actual transfer. A complete insider threat detection program needs both, because the risk operates on two separate timelines: the weeks of behavioral indicators that precede a major incident, and the specific moment sensitive data moves off the network.
A network DLP solution operating at the session level, rather than the packet level, captures what is actually contained in a communication: the file content, the destination, and whether the content matches policy restrictions on regulated categories like intellectual property, customer PII, or financial records. Packet-level inspection cannot do this. Individual packets do not carry readable content context. Session-depth visibility is required to understand what is being transferred and whether it should be.
Protocol coverage matters just as much as inspection depth. Insiders who know that standard channels are monitored will use non-standard ones. Protocol-agnostic monitoring across all network ports, combined with encrypted traffic decryption, closes the gaps that selective coverage leaves open.
Fidelis Network® Data Loss Prevention applies patented Deep Session Inspection® technology across all 65,535 network ports, extracting metadata from more than 300 protocol attributes at session depth. It doesn’t generate alerts for analysts to review after a transfer completes. It terminates sessions that violate policy in real time before the data reaches its destination. For negligent insider incidents specifically, that capability changes the outcome entirely: the employee who unknowingly tries to send a file containing regulated data to a personal email account doesn’t become a breach statistic if the transfer is blocked at the network layer before it arrives.
How to Build a Robust Insider Threat Program
On January 28, 2026, CISA published updated guidance6 on assembling multi-disciplinary insider threat management teams, built around a four-phase POEM framework: Plan, Organize, Execute, and Maintain. The central point was unambiguous. Insider threat management is a continuous organizational capability, not a technology deployment you configure once and leave running.
Acting CISA Director Madhu Gottumukkala was direct about the stakes: “Insider threats remain one of the most serious challenges to organizational security because they can erode trust and disrupt critical operations.” The guidance calls specifically for teams that span security, legal, HR, and operations, with structured escalation paths from monitoring signal to investigation to response. Technology is one component. The human processes around it determine whether it actually works.
The Ponemon 2025 data shows this kind of investment is starting to produce measurable results. Organizations doubled their insider risk budget allocation, from 8.2% to 16.5% of total IT security spend, in a single year. Containment times dropped from 86 to 81 days, the first year-over-year decrease in the report’s history. These aren’t coincidental trends. They’re what happens when organizations start treating insider risk as a formal program rather than an afterthought addressed only after something has already gone wrong.
A program built to detect threats early, rather than react to them after the fact, requires:
Defined inventory of critical assets and sensitive data
Behavioral baselines per role, team, and access tier
Real-time alerts on anomalous data access and transfers
Session-level network inspection across all protocols
Privileged user monitoring with session-level recording
DLP enforcement that blocks transfers, not just flags them
Integration across DLP, UEBA, and SIEM platforms
Periodic access rights reviews and least-privilege enforcement
Defined escalation path from alert to investigation to response
Security awareness training tied to observed behavioral patterns
The financial math here is not complicated. Ponemon’s data shows organizations spend $211,021 per incident on containment versus just $37,756 on monitoring. Incidents contained within 31 days average $10.6 million in total cost. Those that extend beyond 91 days average $18.7 million. That $8 million gap is the return on a monitoring investment that detects faster. It is not a theoretical benefit, but a documented cost differential across hundreds of real incidents.
What insider threat monitoring ultimately reveals is not just a list of incidents or suspicious users. It reveals the gaps that were already there: access that was never properly scoped, data that was never tracked, and channels that were never watched. Seeing those gaps is the prerequisite for closing them. Closing them before an incident occurs is the only version of insider risk management that actually protects an organization’s most critical assets before the damage is done.
Assess Your Current Data Protection Coverage
The Fidelis DLP Evaluation Assessment helps security teams identify gaps in data movement visibility and network-level enforcement before an incident surfaces them first.
Frequently Ask Questions
What does insider threat monitoring actually reveal in most organizations?
Insider threat monitoring typically reveals four categories of hidden risk: overprivileged accounts with access that was never revoked, sensitive data moving through unmonitored channels, shadow data in locations security teams did not know about, and pre-incident behavioral patterns that appear weeks before a breach occurs.
What is the average cost of an insider threat incident in 2026?
The 2026 Ponemon Cost of Insider Risks Global Report found the average annual cost of insider security incidents reached $19.5 million per organization. North American organizations average $22.2 million annually. Incidents contained in under 31 days cost $10.6 million on average, while those exceeding 91 days cost $18.7 million.
What causes most insider threat incidents?
According to Ponemon Institute 2025 research, 55% of insider incidents are caused by employee negligence, 25% by malicious insiders, and 20% by credential theft. Negligence is the most common driver by volume, making detection and enforcement at the network layer critical for the majority of cases.
How does behavioral analytics help detect insider threats?
User and entity behavior analytics (UEBA) builds baselines from historical user activity and flags deviations that static access policies cannot detect. When a user’s data access patterns, transfer volumes, or system usage shift materially from their established baseline, especially across multiple indicators simultaneously, the system surfaces it for investigation before the activity reaches the point of confirmed damage.
What is the difference between insider threat monitoring and data loss prevention?
Insider threat monitoring tracks user behavior, access patterns, and activity signals to identify risk before data moves. Data loss prevention (DLP) operates at the network or endpoint layer to detect and block unauthorized transfers of sensitive data in real time. An effective insider threat program uses both: behavioral monitoring for early detection and DLP for enforcement at the point of transfer.
The post What Insider Threat Monitoring Reveals About Hidden Organizational Risk appeared first on Fidelis Security.
No Responses