How CryptoBind’s Encryption Suite Addresses DPDP Act Requirements
India’s Digital Personal Data Protection (DPDP) Act, 2023 is no longer a distant legislative horizon.As enforcement […]
The DPDP Act 2023: A Complete Compliance Guide for Indian Enterprises
The Digital Personal Data Protection (DPDP) Act 2023 of India is a watershed moment in the […]

Anthropic Mythos spurs White House to weigh pre-release reviews for high-risk AI models
The Trump administration is in early discussions about whether advanced AI models should be vetted before […]
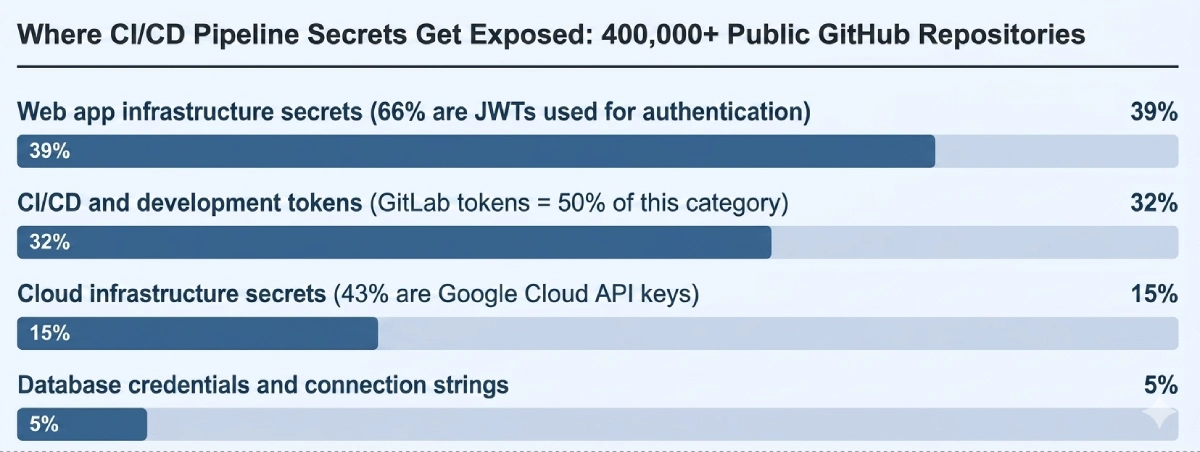
CI/CD Pipeline Security Tools and Technologies
Key Takeaways CI/CD security requires stage-specific tools; no single platform covers the full pipeline risk surface. […]
‘Patch Wave’ Warning: AI May Expose Decades of Hidden Software Bugs
The UK’s National Cyber Security Centre issued an unusual warning about what’s coming next. AI, the […]
Security agencies draw red lines around agentic AI deployments
With prompt injection and other attack pathways consistently surfacing across agentic AI deployments, security watchdogs have […]

The fake IT worker problem CISOs can’t ignore
Hiring fake IT workers has been a growing problem in recent years — but it’s often […]

How CISOs should utilize data security posture management to inform risk
Every CISO eventually faces the same tension: You know your security program needs to mature, but […]

Was ist ein Botnet?
Ein Botnetz besteht aus vielen “Zombie”-Rechnern und lässt sich beispielsweise einsetzen, um DDoS-Attacken zu fahren. Das […]
What is XDR (Extended Detection and Response) in Cybersecurity? A Quick Guide
Extended Detection and Response (XDR) Explained Extended Detection and Response (XDR) is a comprehensive security solution […]
