Key Takeaways
CI/CD security requires stage-specific tools; no single platform covers the full pipeline risk surface.
Secrets exposure remains a primary breach vector, with long remediation windows actively exploited
SAST, SCA, DAST, and IAST each address distinct vulnerability layers and must be combined
Artifact integrity through signing and SLSA provenance prevents build and deployment tampering
Runtime monitoring (CNAPP) is critical as risk continues evolving after deployment
Enforcing blocking security gates and least privilege access directly reduces exploitability
CI/CD pipeline security is not a single tool decision. The pipeline spans source code, build systems, container registries, infrastructure configs, and production workloads. Each stage carries different risks and needs different controls. This guide covers the full stack of ci/cd pipeline security tools, the industry standards that govern them, and the CI/CD security best practices that make them work in production.
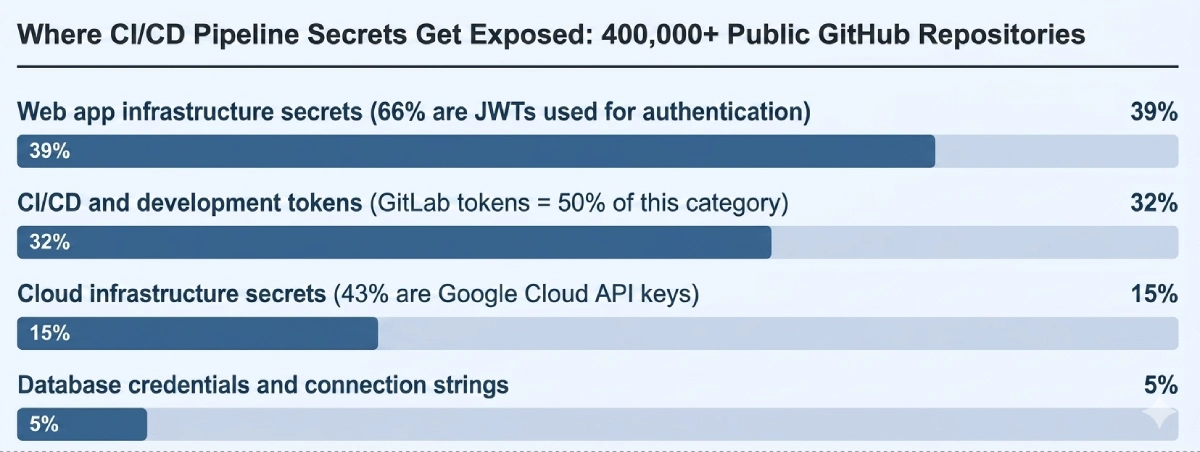
The Datadog State of DevSecOps Report 20261 found 87% of organizations running at least one known exploitable vulnerability in production. The Verizon 2025 Data Breach Investigations Report2 found CI/CD tokens account for 32% of all secrets exposed in public repositories, with a 94-day median time to fix. That is a three-month open window while attackers run automated credential scanners against public repos around the clock.
87% of organizations have at least one known exploitable vulnerability in deployed services
32% of all exposed public repo secrets are CI/CD and development tokens
71% of GitHub Actions workflows left completely unpinned
94 days median time to remediate a leaked CI/CD secret in a public repository
CI/CD Pipeline Security Tools by Stage
Each stage of a CI/CD pipeline introduces a distinct risk. Source code has logic flaws. Dependencies carry known CVEs. Build systems can be tampered with. Container images carry OS-level vulnerabilities. Infrastructure-as-code files contain misconfigurations. Deployed workloads keep accumulating risk after launch. No single platform covers all of this. The CI/CD security tools below address each stage specifically.
SAST
Static Application Security Testing runs static code analysis against source code before any execution. Finds hardcoded sensitive data, insecure patterns, injection vulnerabilities, and security flaws early in development, where remediation costs the least.
SCA
Software Composition Analysis audits third-party libraries and open-source components against CVE databases and the CISA KEV catalog3. Only 21% of organizations have full dependency visibility. SCA closes that gap directly.
DAST
Dynamic Application Security Testing tests running applications for vulnerabilities static analysis cannot catch: authentication bypasses, injection flaws, broken session handling. SAST operates on code. DAST operates on behavior. Both are needed.
IAST
Interactive Application Security Testing instruments the application during functional test execution. It observes behavior from inside the running process, combining static and dynamic signals. Produces fewer false positives than either SAST or DAST alone.
Secrets Detection
Scans code repositories, pipeline YAML files, container images, and commit history for exposed API keys, tokens, and passwords. Needs to run on every commit and merge, not just at initial push. Secrets surface through automated merges and dependency updates too.
Secrets Management
Replaces static credentials in pipeline configs with short-lived secrets fetched at runtime from a vault. Eliminates the root cause behind the 94-day credential exposure window: long-lived tokens that sit in environment variables and config files indefinitely.
Container Scanning
Scans container images for known vulnerabilities in OS packages and application libraries before the image reaches a registry. Stops images with active CVEs from entering production workloads.
Image Signing
Creates cryptographic attestations that tie a container image to its verified build provenance. Admission controllers can then reject unsigned images at deploy time, blocking artifact substitution before execution.
IaC Scanning
Infrastructure as Code security scanning detects misconfigurations in Terraform, Kubernetes manifests, CloudFormation, and Helm charts before deployment. Overly permissive IAM roles and open security groups are far cheaper to fix while they are still text files.
CNAPP
Cloud-Native Application Protection Platforms carry security posture past the pipeline into production. CSPM covers cloud configuration. CWPP covers running workloads. Continuous monitoring after deployment keeps the organization’s security posture accurate beyond what build-time scanning can provide.
SAST vs. DAST vs. IAST: Static code analysis finds what is wrong in source code. Dynamic testing finds what is exploitable in the running application. Interactive testing observes real execution during functional tests. Each covers a distinct vulnerability surface. Using only one type means predictable blind spots in application security.
CI/CD Pipeline Security Standards: NIST, SLSA, and OWASP
Several authoritative frameworks govern how to secure a CI/CD pipeline at both governance and technical levels. They appear in compliance audits, federal software procurement requirements, and vendor security assessments. Each one covers a different layer.
FrameworkWhat It CoversApplies To
NIST SP 800-204D
csrc.nist.govDevSecOps strategies for software supply chain security in CI/CD; build integrity, dependency controls, SBOM requirements, attestations, and secure infrastructure deployments throughout the pipelineFederal agencies and contractors; the most specific US government guidance available for CI/CD build and deploy securityNIST SSDF SP 800-218
csrc.nist.govSecure Software Development Framework covering the entire software development life cycle: source code protection, code repositories, third-party components, and the full development process from design through deploymentMandatory under Executive Order 14028 for software vendors supplying the US federal government; baseline for any organization that needs formal SDLC governanceSLSA
slsa.devSupply-chain Levels for Software Artifacts; four-level maturity model for build integrity and provenance; higher levels require tamper-resistant build environments and cryptographically signed attestations verifying what was built, when, and by whomEngineering teams hardening CI/CD against supply chain attacks; SLSA Level 2, which uses a hosted build platform with signed provenance, is the practical starting point for most organizationsOWASP CI/CD Top 10
owasp.orgTen most critical CI/CD security risks with specific mitigations per pipeline stage; covers insufficient flow control mechanisms, poisoned pipeline execution, improper artifact integrity validation, and insufficient access controlsDevelopment and operations teams; maps directly to pipeline configuration choices and works as an actionable checklist alongside NIST governance frameworks
NIST SP 800-218 defines what the development process must achieve. OWASP CI/CD Top 10 translates those goals into specific pipeline controls. SLSA provides the cryptographic verification layer for build integrity and artifact provenance. Together: governance, implementation, and verification.
CI/CD Pipeline Security Best Practices: How to Secure Your Pipeline
The practices below address the gaps threat data identifies as most actively exploited. Each maps directly to the tool categories above.
Pin workflow actions and dependencies to a specific commit SHA
When a pipeline references actions/checkout@v4, it runs whatever code sits at that tag at execution time. A compromised maintainer account can move the tag silently. The pipeline then runs attacker-controlled code on its next trigger, with no change visible in any workflow file.
Pinning to a full SHA like actions/checkout@11bd71901bbe5b1630ceea73d27597364c9af683 guarantees execution matches what was reviewed and approved. The Xygeni GitHub Action compromise of March 2026 exploited this exact pattern: stolen credentials moved a mutable tag to a backdoored commit, hitting every repository that referenced it. Same fix either way: one line per action, zero cost.
Turn security scans into blocking pipeline gates
When a SAST scan flags a critical vulnerability and the build passes anyway, developers learn those alerts do not matter. In pipelines moving fast, non-blocking warnings get ignored systematically. Advisory-only security checks in CI/CD do not change behavior.
High-severity, exploitable findings from static application security testing, software composition analysis, and IaC scanning should stop the build. Medium severity gets a warning. Everything else gets logged. The blocking gate creates the decision point at the stage where remediation is cheapest.
Replace static credentials with short-lived tokens
API keys stored as CI/CD environment variables accumulate. Most never get rotated. The Verizon 2025 DBIR found a 94-day median remediation window for secrets found in public repositories. Keys that were never flagged have no remediation timeline at all.
OIDC workload identity federation removes the stored credential entirely. GitHub Actions and GitLab CI support it natively: the platform issues a short-lived, job-scoped token that expires after execution. Nothing to steal because nothing persists. HashiCorp Vault, AWS Secrets Manager, and Azure Key Vault handle dynamic secret injection for services that cannot use OIDC directly.
Sign build artifacts and validate them before deployment
An unsigned container image in a registry has no cryptographic connection to the build that created it. Between registry push and cluster pull, it can be swapped for a malicious version.
Signing artifacts with Cosign and generating SLSA provenance attestations creates a verifiable chain from source commit to running container. Admission controllers like Kyverno or OPA Gatekeeper enforce that only signed, attested images reach production. Artifact substitution goes from undetectable to blocked at the gate.
Generate a Software Bill of Materials at every build
The median production library runs 278 days behind its latest major version, per the Datadog DevSecOps Report 20261. Libraries from 2023 carry 3.8 average vulnerabilities per service. When a new CVE drops for something three dependency levels deep, organizations without a Software Bill of Materials find out which services are affected by auditing every codebase manually.
Generating an SBOM in CycloneDX or SPDX format at build time and wiring it into continuous CVE monitoring turns “are we affected?” from a days-long exercise into a query that returns in seconds.
Apply role-based access control to every pipeline identity
Pipeline service account permissions grow through additions that never get removed. A job that compiles source code does not need write access to production systems, but many carry it anyway. The Cloud Security Alliance State of SaaS Security Report 20254 found 46% of organizations cannot monitor their non-human identities.
Every oversized permission is post-compromise lateral movement waiting to happen. Scoping each job to minimum required access and reviewing pipeline permissions on a regular schedule keeps the blast radius of any compromised credential contained.
Extend security posture from the pipeline into production
Build-time scanning produces a point-in-time result. After deployment, new CVEs get published, configurations drift, and runtime behavior changes. What a pipeline approved six months ago may not reflect the risk profile of what is running today.
CNAPP platforms with CSPM and CWPP capabilities maintain continuous monitoring past the pipeline handoff. Fidelis Halo® integrates with CI/CD workflows via APIs and automation hooks, enabling security and compliance checks to align with deployment processes while extending protection into runtime across AWS, Azure, on-premises, and hybrid environments.
Cloud-friendly Deployment
Hyper-scalable Workload Protection
Agentless Cloud Posture Management
How CI/CD Pipeline Security Tools Work Together
Secure CI/CD pipeline implementation is a layered problem. SAST covers source code flaws. SCA covers third-party library vulnerabilities. Secrets detection and management close the credential exposure window the Verizon DBIR marks as the primary breach vector. Container scanning and image signing chain provenance from build to runtime. IaC scanning catches misconfigurations before infrastructure gets provisioned. CNAPP extends coverage past the deployment boundary into production.
Supply chain attacks on CI/CD pipelines surged in October 2025 to a new record, more than 30% above the previous peak, per Cyble threat data published by Industrial Cyber5. These attacks exploit the gaps between tool categories deliberately. A credential-harvesting payload injected into an npm package gets pulled into builds through automated dependency updates. SCA catches it after the package is cataloged. Runtime monitoring catches the payload when it tries to execute. Neither method stops the full chain on its own. Running both does.
Several platform-level controls also strengthen overall pipeline security posture without requiring additional tools:
Branch protection with required code review on all build-triggering branches closes the insufficient flow control mechanisms risk defined in OWASP CI/CD SEC-1
Environment-scoped secrets prevent staging pipelines from accessing production credentials and vice versa
Commit signing creates a verified identity record for every code change entering a repository
IaC scanning as a blocking pre-deploy check catches misconfigurations in Terraform and Kubernetes manifests before they are applied
Pipeline alerts wired to SIEM and SOAR enable automated containment; the window between credential compromise and active damage is minutes
The post CI/CD Pipeline Security Tools and Technologies appeared first on Fidelis Security.
No Responses