
5 ways to strengthen identity security and improve attack resilience
Identity compromise has become one of the most effective ways for attackers to infiltrate business systems. […]
How Can Active Deception Validate Security Controls in Real Environments?
Key Takeaways Active deception security helps organizations validate whether existing security controls are actually working. Deception […]
Zero‑click Grafana AI attack can enable enterprise data exfiltration
Indirect prompt injection is possible on AI-powered dashboards, allowing exfiltration of sensitive enterprise data without user […]
Building secure AI data pipelines with CryptoBind
Artificial Intelligence (AI) is as reliable as the data that it ingests. With enterprises broadening their […]
Microsoft says Medusa-linked Storm-1175 is speeding ransomware attacks
Microsoft has warned that Storm-1175, a cybercrime group linked to Medusa ransomware, is exploiting vulnerable web-facing […]

Supply chain security is now a board-level issue: Here’s what CSOs need to know
For many years, supply chain security was viewed purely as a technical concern. However, with high-profile […]

The rise of proactive cyber: Why defense is no longer enough
For more than two decades, cybersecurity has been built on a reactive model: detect intrusions, patch […]

The noisy tenants: Engineering fairness in multi-tenant SIEM solutions
I recently had the opportunity to review five popular SIEM solutions as part of a judging […]
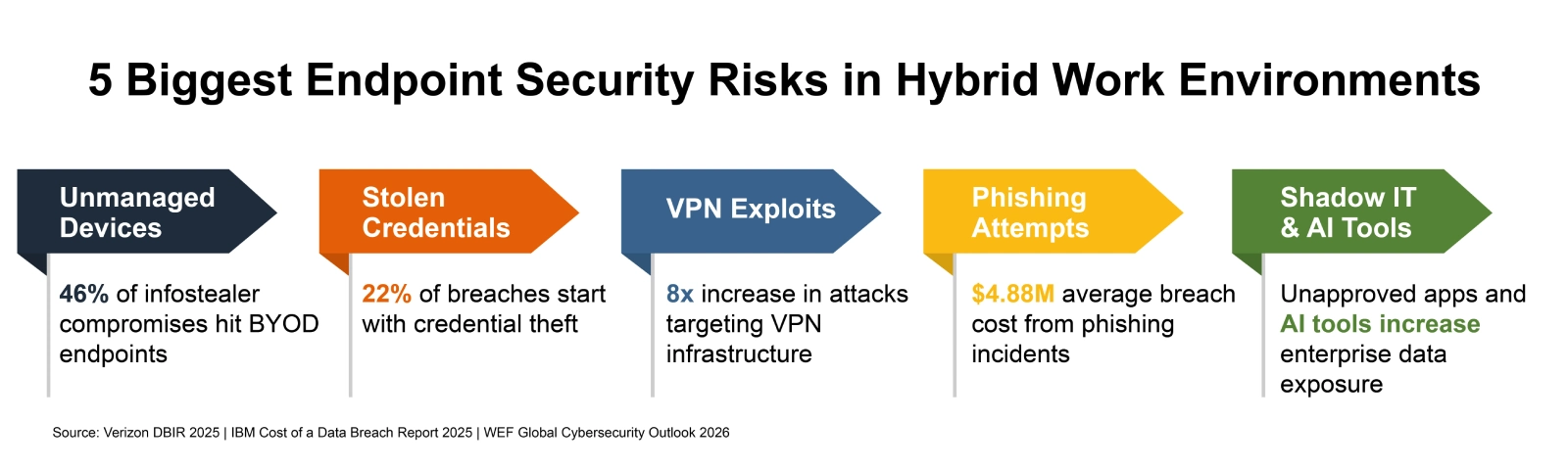
How to Secure Endpoints in Hybrid Work Environments
Picture a Tuesday morning at any mid-size U.S. company. A sales rep logs into Salesforce from […]
Microsoft Unveils $10B Plan to Scale AI, Cloud, and Cybersecurity in Japan
Microsoft is doubling down on Japan as a key market in the global artificial intelligence race, […]
