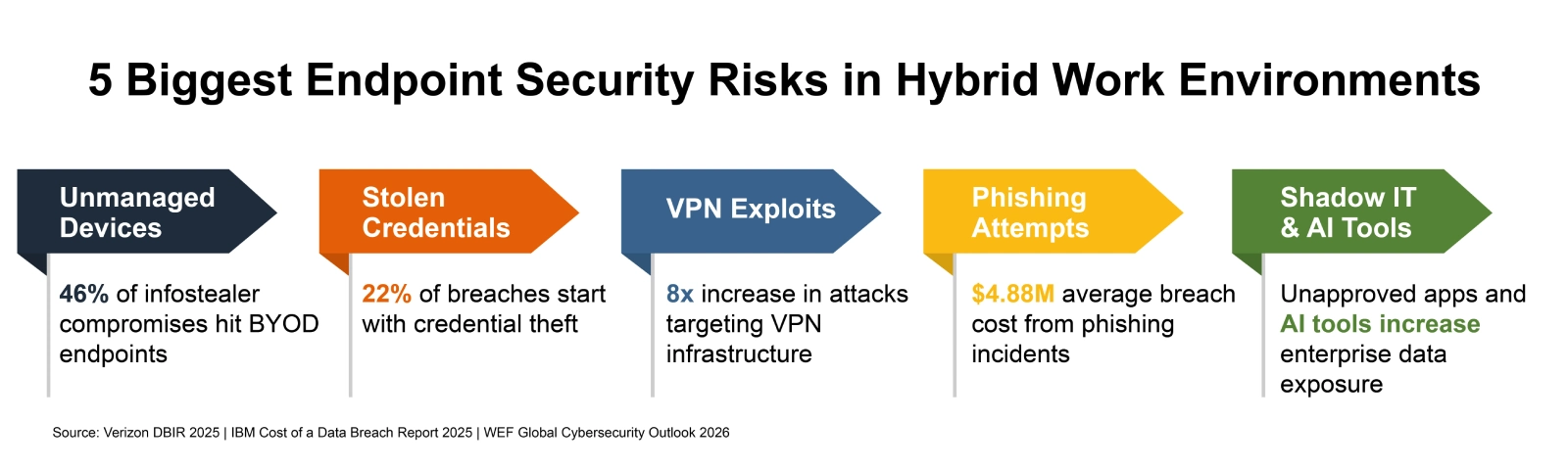
How to Secure Endpoints in Hybrid Work Environments
Picture a Tuesday morning at any mid-size U.S. company. A sales rep logs into Salesforce from […]
Microsoft Unveils $10B Plan to Scale AI, Cloud, and Cybersecurity in Japan
Microsoft is doubling down on Japan as a key market in the global artificial intelligence race, […]

North Korean hackers abuse LNKs and GitHub repos in ongoing campaign
DPRK-linked threat actors are preferring stealth over sophistication in targeting South Korean organizations, as researchers report […]

Authentication is broken: Here’s how security leaders can actually fix it
Authentication keeps breaking where it matters most: On regulated front lines such as healthcare, government, aerospace […]

6 ways attackers abuse AI services to hack your business
Attackers are starting to exploit AI systems to mount attacks in the same way they once […]

Escaping the COTS trap
Over the years, enterprise cybersecurity environments have accumulated staggering numbers of commercial tools. Industry research converges […]