The democratization of AI data poisoning and how to protect your organization
Smart organizations have spent the last three years protecting their AI tools from skilled prompt injection-style […]
How to Rewrite Your Privacy Notice for DPDP Compliance
As the Digital Personal Data Protection Act moves into active enforcement, many organisations across India are […]

Why key management becomes the weakest link in a post-quantum and AI-driven security world
When people talk about cryptography, they usually talk about algorithms. RSA versus ECC. Classical versus post […]

5 key trends reshaping the SIEM market
Security information and event management (SIEM) platforms have evolved far beyond their basic log collection and […]

Security-Infotainment: Die besten Hacker-Dokus
Sie fühlen sich leer ohne Security-Dashboard? Diese Dokumentationen überbrücken den Schmerz bis zum nächsten Arbeitstag. Foto: […]

Hackers turn bossware against the bosses
A threat actor is abusing an employee monitoring application and a remote monitoring and management platform […]

Why identity recovery is now central to cyber resilience
Ransomware has permanently changed how security leaders think about risk. Verizon’s 2025 Data Breach Investigations Report […]

Unplug to Recharge: 5 Digital Detox Tips for Better Mental Health in 2026 🧘♂️✨
Think back to the last time you sat in silence for ten minutes—no phone, no tablet, […]
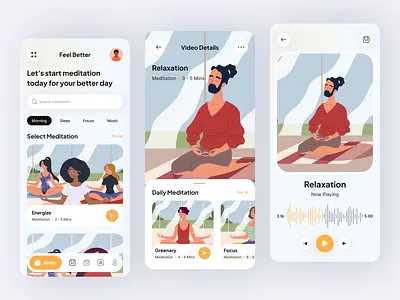
Finding Your Zen: The Best Meditation Apps to Quiet the Noise in 2026 🧘♂️✨
In a world that seems to be moving at 100 miles per hour, finding a moment […]

The Freedom Revolution: Navigating the Best Freelancing Platforms in 2026 🌍✨
The traditional 9-to-5 is no longer the only path to a successful career. We are living […]
