
Google leaks details for Chromium bug that can turn browsers into bots
Chromium — the open-source browser that underpins Google Chrome, Microsoft Edge, and Opera, among others — […]

FBI warns of Kali Oauth stealers
The FBI has warned of the danger from a new wave of phishing attacks generated by […]

Police take down VPN service (this time with a good reason)
European authorities have cracked down on a VPN that has been used for various criminal activities. […]
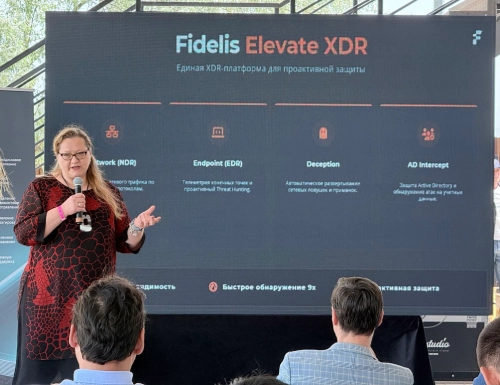
What Makes Fidelis CSPM Enterprise-Ready for Modern Cloud Security?
Key Takeaways Cloud Security Posture Management (CSPM) tools show you what’s going on, but the hard […]

Microsoft says it’s making AI ‘safe for work’ in your browser
Microsoft is testing the addition of agentic AI to its corporate browser, Edge for Business. A […]

Why your AI strategy stops where the PLC starts: Hard lessons from the OT frontlines
I spent two days at a substation connecting a major offshore wind farm to the grid. […]
What I’m Hearing at Security Conferences Worldwide About Ransomware
Across the security conferences I attend in different regions, ransomware continues to come up in almost […]

Identity as the primary attack surface: What modern breaches are really exploiting
The “retro” way “The thing about the old days is… they are the old days” – […]

Google folds CodeMender into agent ecosystem amid push for AI-led AppSec
Google is expanding the role of its CodeMender security agent from autonomous vulnerability remediation toward a […]

Critical vulnerability in Cisco Secure Workload rated at maximum severity
A critical vulnerability in the on-premises version of the Cisco Secure Workload security platform could allow […]
