Microsoft disrupts malware code-signing service used by ransomware gangs
Microsoft has disrupted the infrastructure powering the largest malware code-signing service used to help ransomware groups […]

Contractor’s public GitHub account exposed GovCloud and CISA credentials
Until a few days ago, a publicly-accessible GitHub repository exposed credentials for both US government AWS […]
AntV data visualization tool the latest to be hit by ongoing npm supply chain attacks
The world’s largest open-source registry, node package manager (npm), has been hit by another fast-moving malware […]

GitHub scales back bug bounties, reminds users security is their responsibility too
Faced with the growing volume of submission to its bug bounty program, GitHub is replacing cash […]
The New Malware Playbook and How EDR Must Adapt
Key Takeaways The malware playbook of the new era is centered on stealth, fileless attacks, and […]

Internet Explorer may be dead, but its ghost still runs malware
Microsoft’s aging “mshta.exe” utility, a leftover component from Internet Explorer, is still being actively abused in […]
Why HSMs Are Central to Any Quantum-Safe Migration Strategy
In August 2024, NIST finalised its first set of post-quantum cryptographic standards, ML-KEM, ML-DSA, and SLH-DSA, […]

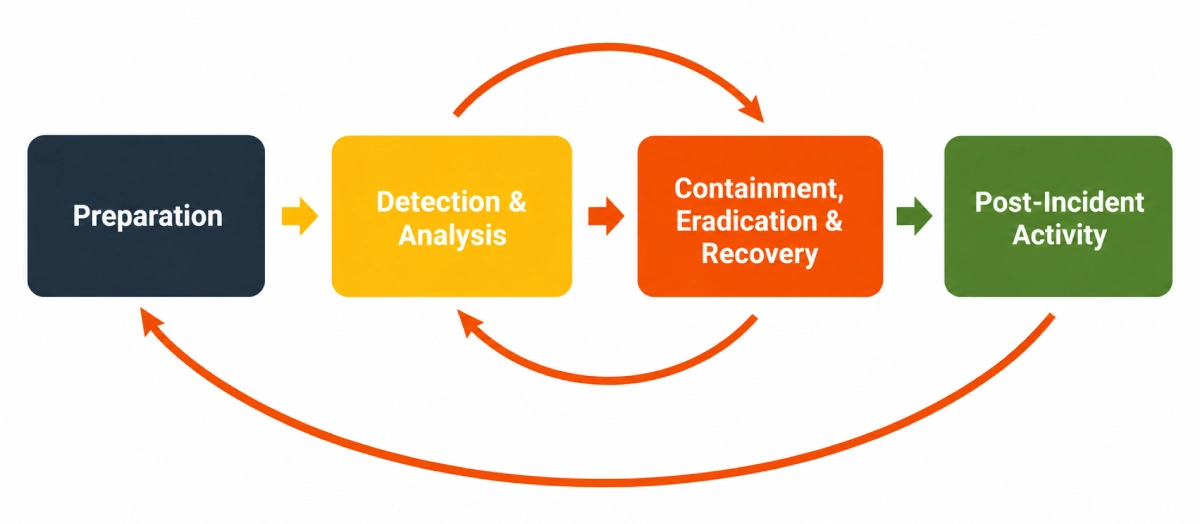
7 tips for accelerating cyber incident recovery
Despite strong and redundant defenses, enterprises remain vulnerable to a wide range of cyberattacks. And because […]

SIEM-Kaufratgeber
Die kontextuellen Daten, die SIEM-Lösungen liefern, sind eine grundlegende Komponente moderner Security-Stacks. PeopleImages.com – Yuri A […]

Schwachstellen managen: Die besten Vulnerability-Management-Tools
Schwachstellen zu managen, muss keine Schwerstarbeit sein. Wenn Sie die richtigen Tools einsetzen. Das sind die […]
