Unauthorized Group Gains Access to Anthropic’s Mythos AI
Anthropic is investigating reports that an unauthorized group gained access to its restricted Mythos AI cybersecurity […]
How to Detect & Prevent Remote Code Execution (RCE)
Key Takeaways RCE lets attackers execute arbitrary code remotely and quickly escalate privileges. Detecting RCE requires […]
NSA Reportedly Uses Anthropic’s Mythos AI Despite ‘Supply Chain Risk’ Designation
The National Security Agency (NSA) is reportedly using Anthropic’s new most powerful AI model, Mythos Preview, […]
OpenAI Debuts GPT-5.4-Cyber, a Locked-Down AI Model for Cyber Defense
Cyber defense just got sharper… but the gate just got tighter. OpenAI has introduced GPT-5.4-Cyber, a […]
Anthropic Briefed Trump Administration on Mythos Cyber Capabilities
Anthropic briefed senior Trump administration officials on its new Mythos model before giving outside organizations access, […]
AI Is Exposing a Skills Gap in Cybersecurity Hiring
Artificial intelligence is rapidly transforming cybersecurity roles, but not in the way many expected. Rather than […]
Sybil Attacks Explained: How They Work and Why They Matter
Key Takeaways Sybil attacks exploit systems where identity creation is cheap and unverified, allowing attackers to […]
Project Glasswing: Anthropic Unites Apple, Google, Microsoft on AI Cybersecurity
In a move that would have seemed unlikely just a few years ago, some of the […]
How Can Active Deception Validate Security Controls in Real Environments?
Key Takeaways Active deception security helps organizations validate whether existing security controls are actually working. Deception […]
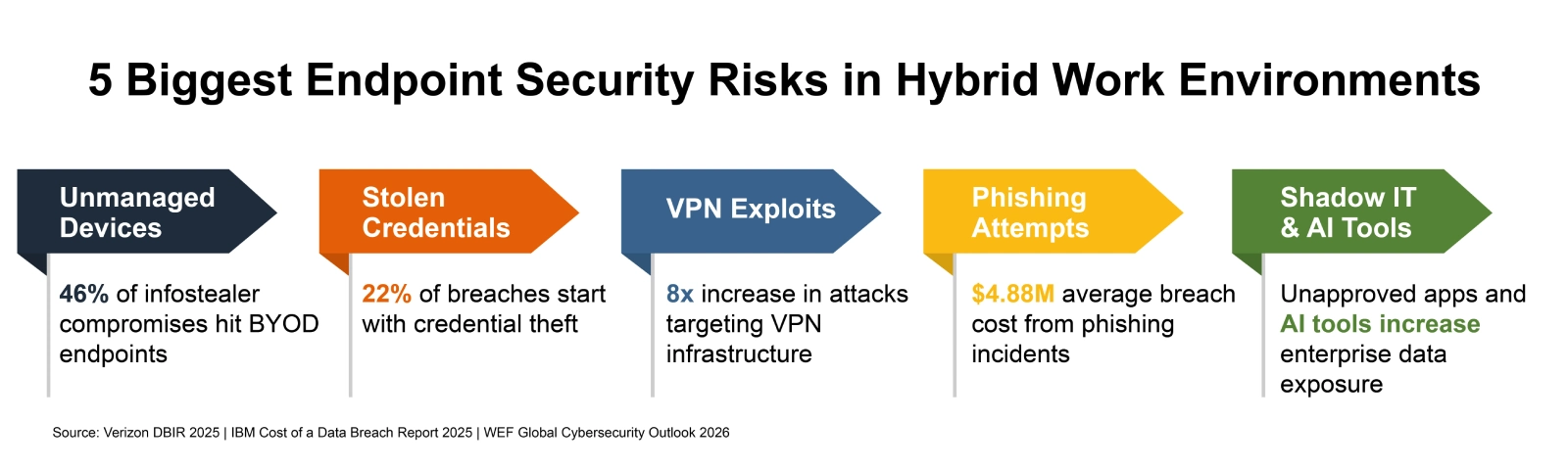
How to Secure Endpoints in Hybrid Work Environments
Picture a Tuesday morning at any mid-size U.S. company. A sales rep logs into Salesforce from […]