
Ransomware gang going after improperly patched SonicWall firewalls
Vulnerable SonicWall firewalls that should have been patched a year ago for an access control vulnerability […]

Microsoft under fire: Senator demands FTC investigation into ‘arsonist selling firefighting services’
US Senator Ron Wyden has formally requested that the Federal Trade Commission investigate Microsoft for what […]

Docker malware breaks in through exposed APIs, then changes the locks
A newly discovered strain of a cryptomining malware, first reported in June 2025, has evolved to […]

Docker malware breaks in through exposed APIs, then changes the locks
A newly discovered strain of a cryptomining malware, first reported in June 2025, has evolved to […]
Building Security Operations That Scale and Don’t Burn Out
In the highly connected modern world, security operations (SecOps) teams can be seen as the first […]
Building Security Operations That Scale and Don’t Burn Out
In the highly connected modern world, security operations (SecOps) teams can be seen as the first […]
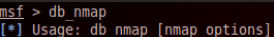
How to hack a website with Metasploit
Normally, a penetration tester or hacker uses Metasploit to exploit vulnerable services in a target server […]
OT security: Why it pays to look at open source
OT security as a strategic success factor Increasing digitalization and networking in industrial production have made […]

AI prompt injection gets real — with macros the latest hidden threat
Attackers are increasingly exploiting generative AI by embedding malicious prompts in macros and exposing hidden data […]

Managed SOC für mehr Sicherheit
Als zentrale Einheit überwachen Fachleute im SOC die gesamte IT-Infrastruktur eines Unternehmens. Rund um die Uhr […]
