
PUMA creeps through Linux with a stealthy rootkit attack
A new loadable kernel module (LKM) rootkit has been spotted in the wild compromising Linux systems […]

How to turn around a toxic cybersecurity culture
A toxic cybersecurity culture affects team turnover, productivity, and morale. Worse yet, it places enterprise systems […]
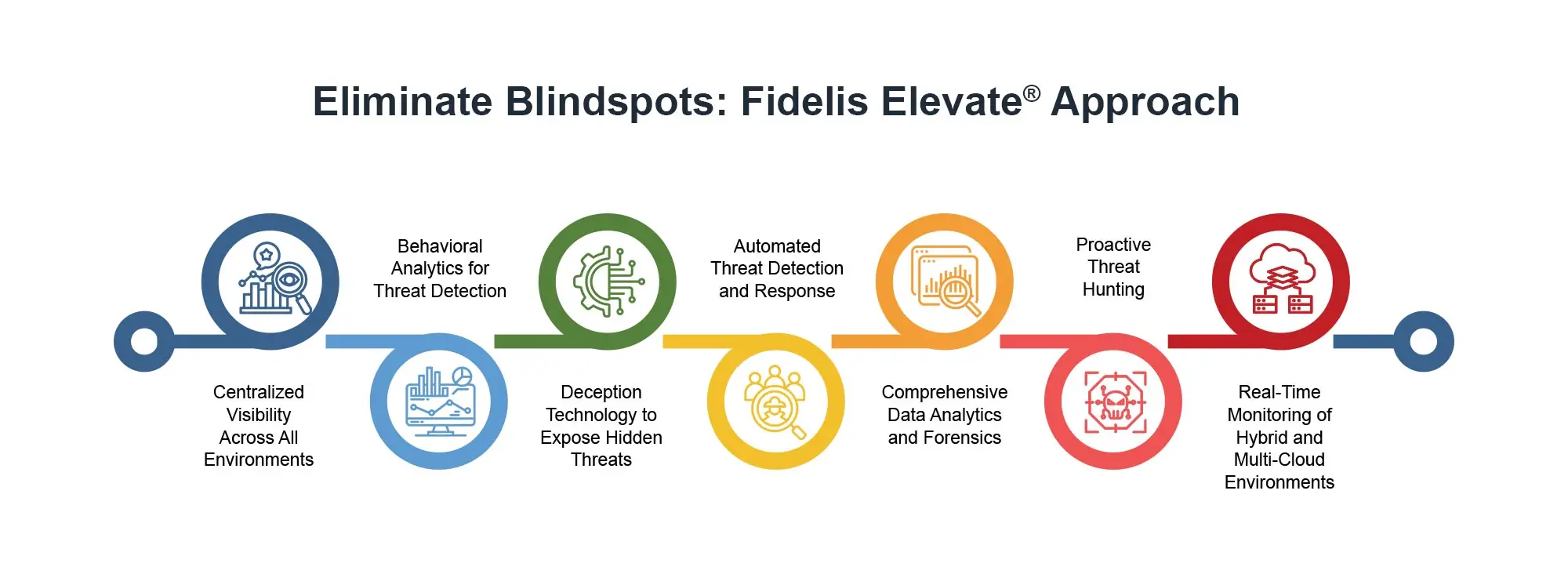
Fidelis Elevate® (XDR): A Proactive Way to Eliminate Blind Spots
The growing complexity of IT environments—across cloud, IoT, and hybrid settings—has ushered in new opportunities for […]
Security researchers find deep flaws in CVSS vulnerability scoring system
The industrywide method for assessing the severity of vulnerabilities in software and hardware needs to be […]

Europol shutters 27 DDoS sites in major crackdown
Europol has announced that it has carried out a major crackdown on cybercriminal actors in cooperation with the […]

Microsoft Windows ‘Best Fit’ character conversion ‘ripe for exploitation’
Security researchers have outlined a novel attack vector that exploits the “Best Fit” character conversion technology […]
Defending Your Active Directory Against Ransomware: Essential Strategies for Protection
Did you know that 59% of organizations have been hit by ransomware, with Active Directory (AD) […]
KeyTrap DNSSEC: The day the internet (almost) stood still
A severe vulnerability in the internet lookup protocol DNSSEC carried the potential to make much of […]

Die wichtigsten Cybersecurity-Prognosen für 2025
Der Cybersecurity-Blick auf 2025. Madcat_Madlove – Shutterstock.com Cyberangriffe auf mehrere deutsche Kliniken oder weltweite IT-Ausfälle durch […]

A security ‘hole’ in Krispy Kreme Doughnuts helped hackers take a bite
Global Doughnut and coffee chain owner Krispy Kreme, famous for its “original glazed doughnuts,” has a […]
