
Chinese ‘Fire Ant’ spies start to bite unpatched VMware instances
Suspected China-aligned actors are running a new “Fire Ant” espionage campaign, active since early 2025, that […]
Fidelis Elevate® Deep Visibility: The Force Multiplier for Modern Security Operations
Security teams struggle to detect and respond to attacks across expanding environments. Cloud systems, digital initiatives, […]
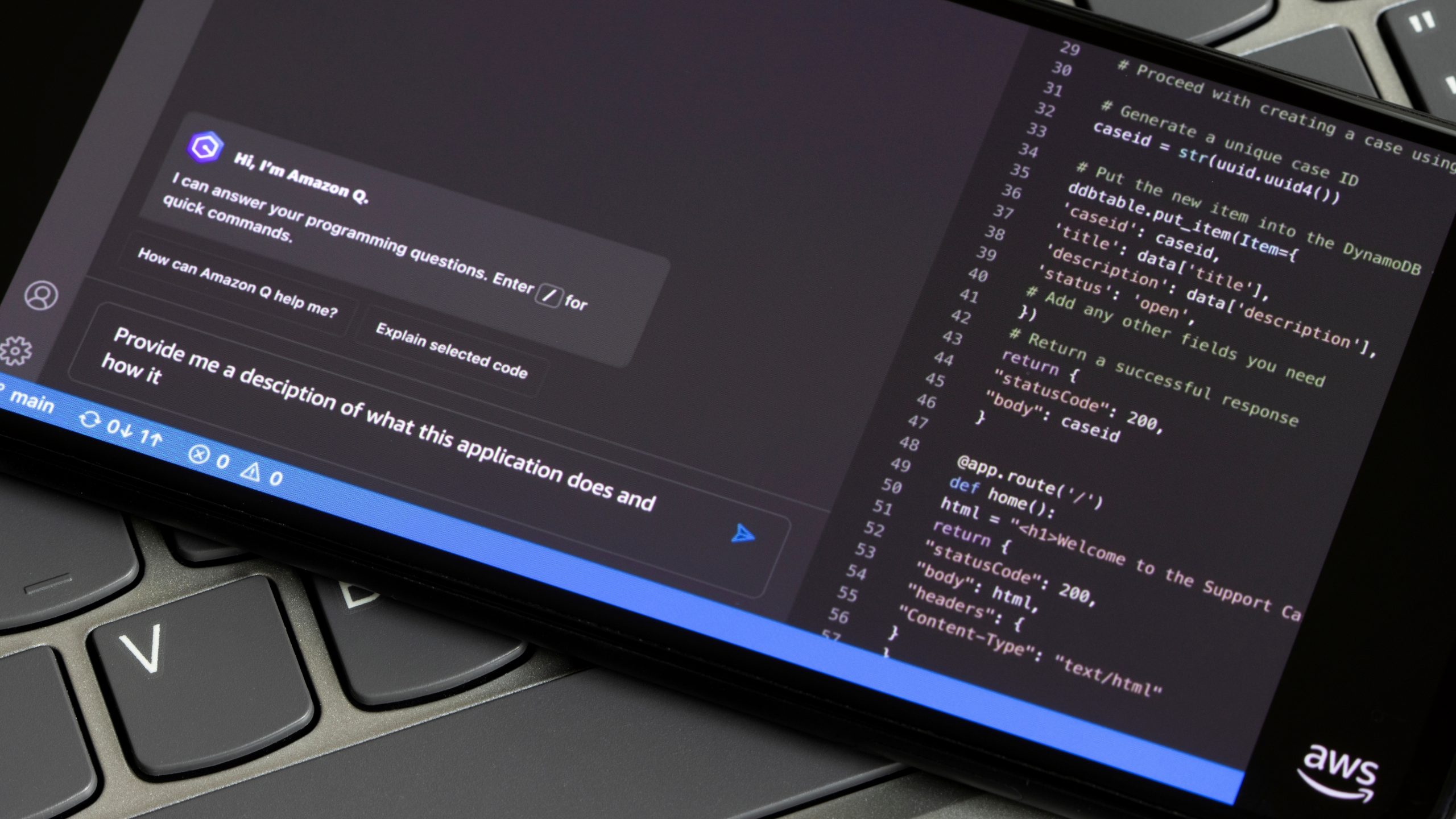
Entwickler-Tool von Amazon verseucht
srcset=”https://b2b-contenthub.com/wp-content/uploads/2025/07/Tada_Images-shutterstock_2395625183-NR_16z9.jpg?quality=50&strip=all 5984w, https://b2b-contenthub.com/wp-content/uploads/2025/07/Tada_Images-shutterstock_2395625183-NR_16z9.jpg?resize=300%2C168&quality=50&strip=all 300w, https://b2b-contenthub.com/wp-content/uploads/2025/07/Tada_Images-shutterstock_2395625183-NR_16z9.jpg?resize=768%2C432&quality=50&strip=all 768w, https://b2b-contenthub.com/wp-content/uploads/2025/07/Tada_Images-shutterstock_2395625183-NR_16z9.jpg?resize=1024%2C576&quality=50&strip=all 1024w, https://b2b-contenthub.com/wp-content/uploads/2025/07/Tada_Images-shutterstock_2395625183-NR_16z9.jpg?resize=1536%2C864&quality=50&strip=all 1536w, https://b2b-contenthub.com/wp-content/uploads/2025/07/Tada_Images-shutterstock_2395625183-NR_16z9.jpg?resize=2048%2C1152&quality=50&strip=all 2048w, https://b2b-contenthub.com/wp-content/uploads/2025/07/Tada_Images-shutterstock_2395625183-NR_16z9.jpg?resize=1240%2C697&quality=50&strip=all 1240w, https://b2b-contenthub.com/wp-content/uploads/2025/07/Tada_Images-shutterstock_2395625183-NR_16z9.jpg?resize=150%2C84&quality=50&strip=all 150w, […]

What to Look for in a Modern EDR Solution: 6 Critical Capabilities
The threat landscape now includes fileless attacks, zero-day exploits, and sophisticated lateral movements that evade signature […]
Speeding Up Vulnerability Remediation Through Threat Correlation in XDR
In cybersecurity, speed matters. But so does clarity. When your organization is facing hundreds or thousands […]

The CISO’s challenge: Getting colleagues to understand what you do
The first-ever CISO, the late Steve Katz, earned the title chief information security officer at Citicorp […]

Darkweb – das verkannte Security-Tool
Ein Besuch im Darkweb kann der IT-Sicherheit zuträglich sein. Postmodern Studio | shutterstock.com Ist vom Darkweb […]
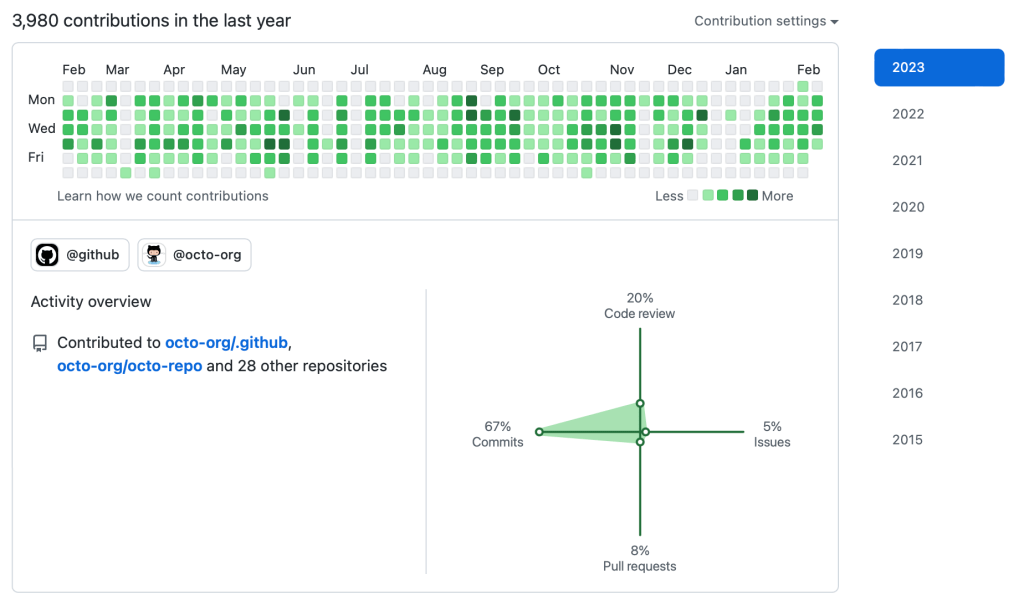
GitHub Recon: The Underrated Technique to Discover High-Impact Leaks in Bug Bounty
When it comes to bug bounty hunting or red teaming, most folks start with the usual […]

AI-forged panda images hide persistent cryptomining malware ‘Koske’
A new malware strain named ‘Koske’ is delivering crypto-mining payloads through dropper files posing as benign […]

Schwarzmarkthändler wollen mit Bots an Tickets kommen
srcset=”https://b2b-contenthub.com/wp-content/uploads/2025/07/shutterstock_2161920885.jpg?quality=50&strip=all 4000w, https://b2b-contenthub.com/wp-content/uploads/2025/07/shutterstock_2161920885.jpg?resize=300%2C168&quality=50&strip=all 300w, https://b2b-contenthub.com/wp-content/uploads/2025/07/shutterstock_2161920885.jpg?resize=768%2C432&quality=50&strip=all 768w, https://b2b-contenthub.com/wp-content/uploads/2025/07/shutterstock_2161920885.jpg?resize=1024%2C576&quality=50&strip=all 1024w, https://b2b-contenthub.com/wp-content/uploads/2025/07/shutterstock_2161920885.jpg?resize=1536%2C864&quality=50&strip=all 1536w, https://b2b-contenthub.com/wp-content/uploads/2025/07/shutterstock_2161920885.jpg?resize=2048%2C1153&quality=50&strip=all 2048w, https://b2b-contenthub.com/wp-content/uploads/2025/07/shutterstock_2161920885.jpg?resize=1240%2C697&quality=50&strip=all 1240w, https://b2b-contenthub.com/wp-content/uploads/2025/07/shutterstock_2161920885.jpg?resize=150%2C84&quality=50&strip=all 150w, […]
