Sora 2 Can Generate SpongeBob, Pikachu, and Other Copyrighted Characters
Sora 2 is being used to generate videos featuring SpongeBob SquarePants, Pikachu, and other copyrighted characters. […]

Red Hat OpenShift AI weakness allows full cluster compromise, warns advisory
Red Hat has updated its OpenShift AI Service after discovering a vulnerability with a CVSS rating […]

Neue Phishing-Variante greift Gmail-Nutzer an
srcset=”https://b2b-contenthub.com/wp-content/uploads/2025/10/shutterstock_2423047525.jpg?quality=50&strip=all 7008w, https://b2b-contenthub.com/wp-content/uploads/2025/10/shutterstock_2423047525.jpg?resize=300%2C168&quality=50&strip=all 300w, https://b2b-contenthub.com/wp-content/uploads/2025/10/shutterstock_2423047525.jpg?resize=768%2C432&quality=50&strip=all 768w, https://b2b-contenthub.com/wp-content/uploads/2025/10/shutterstock_2423047525.jpg?resize=1024%2C576&quality=50&strip=all 1024w, https://b2b-contenthub.com/wp-content/uploads/2025/10/shutterstock_2423047525.jpg?resize=1536%2C864&quality=50&strip=all 1536w, https://b2b-contenthub.com/wp-content/uploads/2025/10/shutterstock_2423047525.jpg?resize=2048%2C1152&quality=50&strip=all 2048w, https://b2b-contenthub.com/wp-content/uploads/2025/10/shutterstock_2423047525.jpg?resize=1240%2C697&quality=50&strip=all 1240w, https://b2b-contenthub.com/wp-content/uploads/2025/10/shutterstock_2423047525.jpg?resize=150%2C84&quality=50&strip=all 150w, […]

Neue Phishing-Variante greift Gmail-Nutzer an
srcset=”https://b2b-contenthub.com/wp-content/uploads/2025/10/shutterstock_2423047525.jpg?quality=50&strip=all 7008w, https://b2b-contenthub.com/wp-content/uploads/2025/10/shutterstock_2423047525.jpg?resize=300%2C168&quality=50&strip=all 300w, https://b2b-contenthub.com/wp-content/uploads/2025/10/shutterstock_2423047525.jpg?resize=768%2C432&quality=50&strip=all 768w, https://b2b-contenthub.com/wp-content/uploads/2025/10/shutterstock_2423047525.jpg?resize=1024%2C576&quality=50&strip=all 1024w, https://b2b-contenthub.com/wp-content/uploads/2025/10/shutterstock_2423047525.jpg?resize=1536%2C864&quality=50&strip=all 1536w, https://b2b-contenthub.com/wp-content/uploads/2025/10/shutterstock_2423047525.jpg?resize=2048%2C1152&quality=50&strip=all 2048w, https://b2b-contenthub.com/wp-content/uploads/2025/10/shutterstock_2423047525.jpg?resize=1240%2C697&quality=50&strip=all 1240w, https://b2b-contenthub.com/wp-content/uploads/2025/10/shutterstock_2423047525.jpg?resize=150%2C84&quality=50&strip=all 150w, […]
DoorDash Creators Program Pays Users for Food Videos
While some competitors might scramble with delivery logistics, DoorDash is hungry for more action and positioning […]
DoorDash Creators Program Pays Users for Food Videos
While some competitors might scramble with delivery logistics, DoorDash is hungry for more action and positioning […]
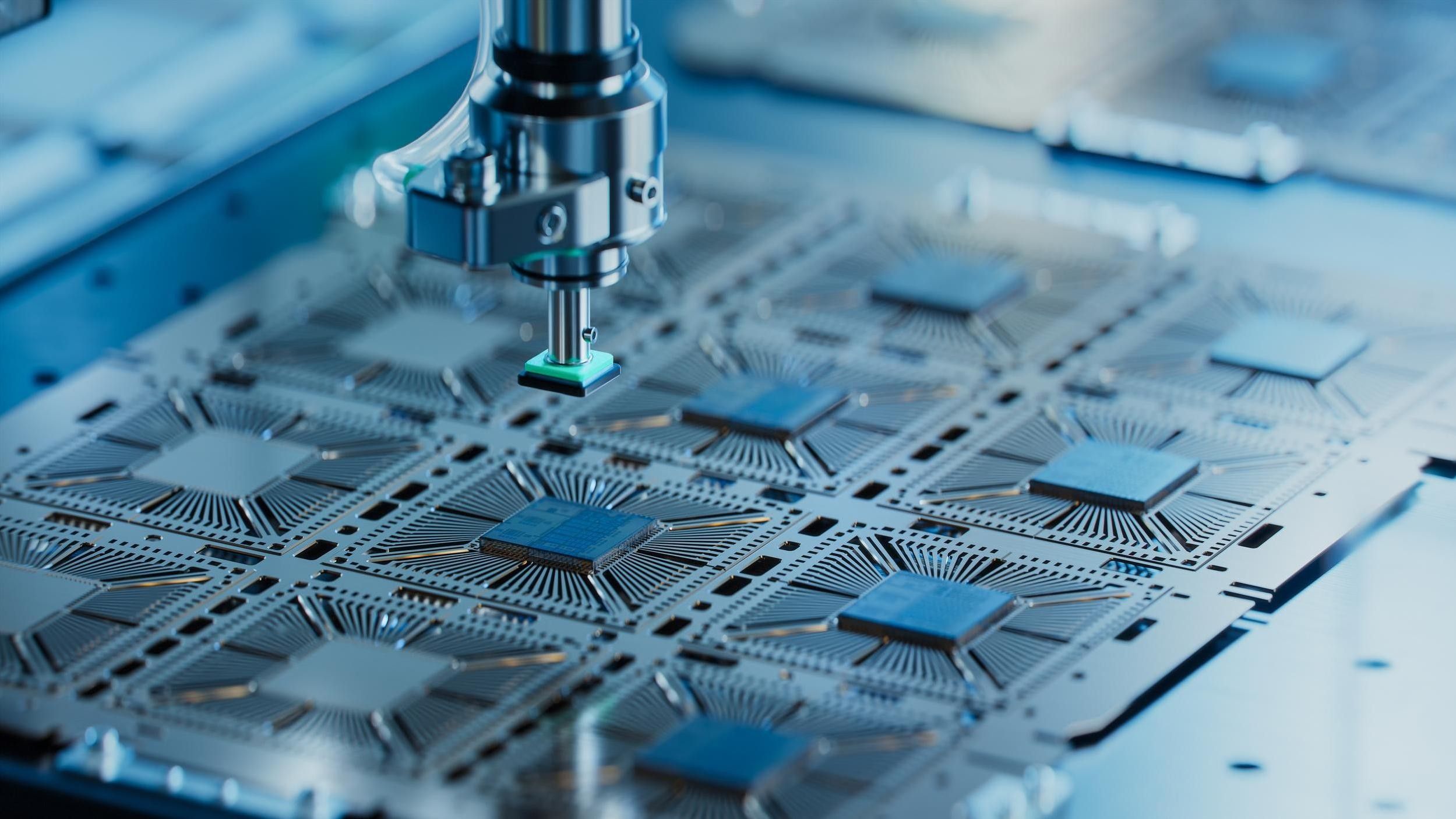
Intel- und AMD-Chips physisch angreifbar
Chips von Intel und AMD sind laut Forschern anfällig für physische Cyberattacken. IM Imagery – shutterstock.com […]

Disaster recovery and business continuity: How to create an effective plan
The core principles of disaster recovery (DR) and business continuity have remained relatively unchanged for decades: […]

That innocent PDF is now a Trojan Horse for Gmail attacks
Enterprise users know by now that they shouldn’t click on suspicious-looking links or download strange files. […]

That innocent PDF is now a Trojan Horse for Gmail attacks
Enterprise users know by now that they shouldn’t click on suspicious-looking links or download strange files. […]
