
CSO Award and Hall of Fame Nominations Open Now
Has your organization pioneered groundbreaking security initiatives that delivered real business value? If so, now is […]

Over 12,000 KerioControl firewalls remain prone to RCE attacks amid active exploits
Businesses around the globe have over 12,000 vulnerable instances of the GFI KerioControl application — a […]
Basic Network Concepts for Hacking
If you’re stepping into the world of ethical hacking, then network knowledge isn’t just helpful but […]
Basic Network Concepts for Hacking
If you’re stepping into the world of ethical hacking, then network knowledge isn’t just helpful but […]

Why security leaders must ensure they have a recovery plan for Active Directory attacks
With mass digitisation and the rising prevalence of global, highly distributed enterprise, cybersecurity leaders must ensure […]

Apple issues emergency patches to contain an ‘extremely sophisticated attack’ on targeted individuals
Apple has rolled out emergency security patches after discovering that an “extremely sophisticated attack” exploited a […]

Top 5 ways attackers use generative AI to exploit your systems
Artificial intelligence is revolutionizing the technology industry and this is equally true for the cybercrime ecosystem, […]

WTF? Why the cybersecurity sector is overrun with acronyms
Back when Elon Musk was best known for founding SpaceX and Tesla, not as one of […]

Die besten DAST- & SAST-Tools
Tools für Dynamic und Static Application Security Testing helfen Entwicklern, ihren Quellcode zu härten. Wir zeigen […]
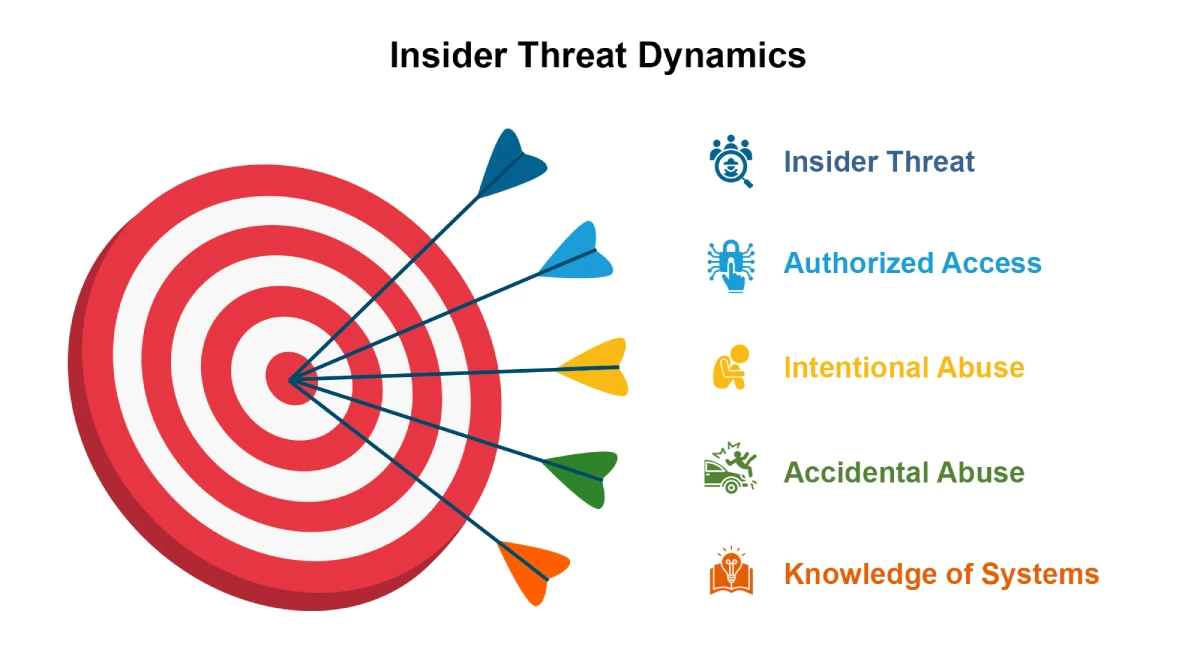
Mitigating Insider Threats with Deception: A Game-Changing Security Approach for 2025
“The greatest information security threat is not from the professional social engineer, nor from the skilled […]
