
Supply chain security is now a board-level issue: Here’s what CSOs need to know
For many years, supply chain security was viewed purely as a technical concern. However, with high-profile […]

The rise of proactive cyber: Why defense is no longer enough
For more than two decades, cybersecurity has been built on a reactive model: detect intrusions, patch […]

The noisy tenants: Engineering fairness in multi-tenant SIEM solutions
I recently had the opportunity to review five popular SIEM solutions as part of a judging […]
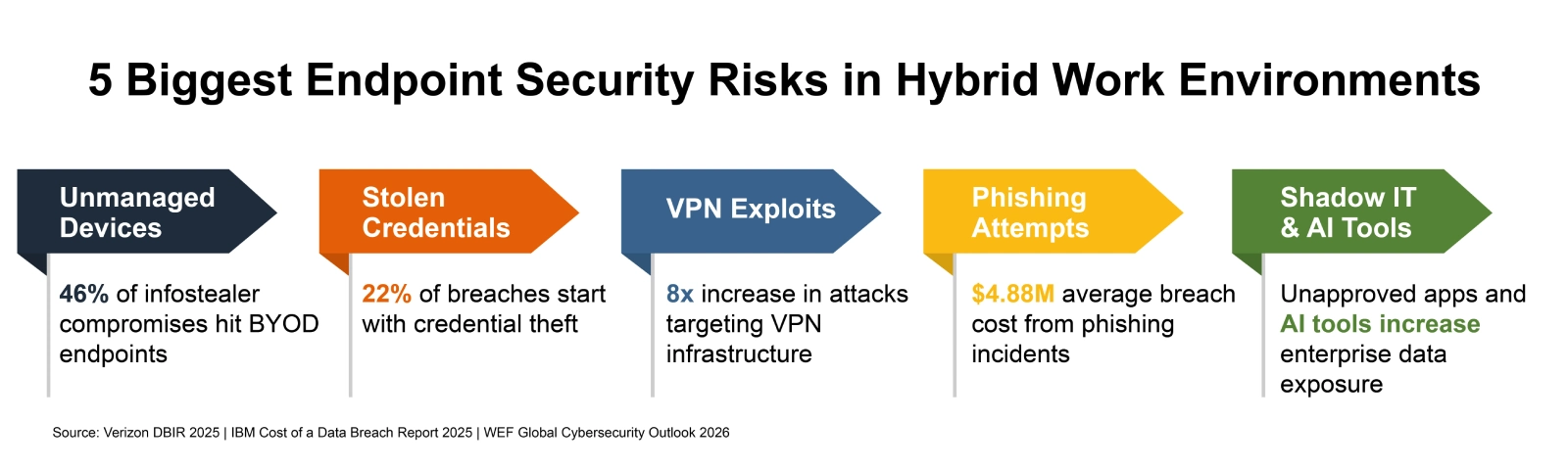
How to Secure Endpoints in Hybrid Work Environments
Picture a Tuesday morning at any mid-size U.S. company. A sales rep logs into Salesforce from […]
Microsoft Unveils $10B Plan to Scale AI, Cloud, and Cybersecurity in Japan
Microsoft is doubling down on Japan as a key market in the global artificial intelligence race, […]

North Korean hackers abuse LNKs and GitHub repos in ongoing campaign
DPRK-linked threat actors are preferring stealth over sophistication in targeting South Korean organizations, as researchers report […]

Authentication is broken: Here’s how security leaders can actually fix it
Authentication keeps breaking where it matters most: On regulated front lines such as healthcare, government, aerospace […]

6 ways attackers abuse AI services to hack your business
Attackers are starting to exploit AI systems to mount attacks in the same way they once […]

Escaping the COTS trap
Over the years, enterprise cybersecurity environments have accumulated staggering numbers of commercial tools. Industry research converges […]

Security lapse lets researchers view React2Shell hackers’ dashboard
An apparent security lapse has allowed researchers to peer into the work of a threat group […]
