AI Actress Stirs Up Hollywood Controversy, Draws Outrage from Union and Stars
It’s not every day that a complete newcomer sets Hollywood abuzz, but Tilly Norwood is no […]
You Can Now Pay for Stuff in ChatGPT, and OpenAI Will Take Its Cut
You can now pay for your shopping directly in ChatGPT. “Instant Checkout” is one of OpenAI’s […]
Newsom Signs SB 53, California’s First Frontier AI Safety Law
California Governor Gavin Newsom has signed SB 53, the Transparency in Frontier Artificial Intelligence Act (TFAIA), […]
Ex-Microsoft Execs Launch AI That Could Kill Excel
Maximor has exited stealth with $9 million in seed funding and a mission to replace finance […]

Datenleck bei Kido-Kindergärten
Eine Ransomware-Bande hat die Daten von mehr als 8.000 Kindern der Kido-Kindergärten gestohlen. New Africa – […]

Databricks enters the cybersecurity arena with an AI-driven platform
Databricks is trying to carve out a bigger role in cybersecurity for itself with the launch […]
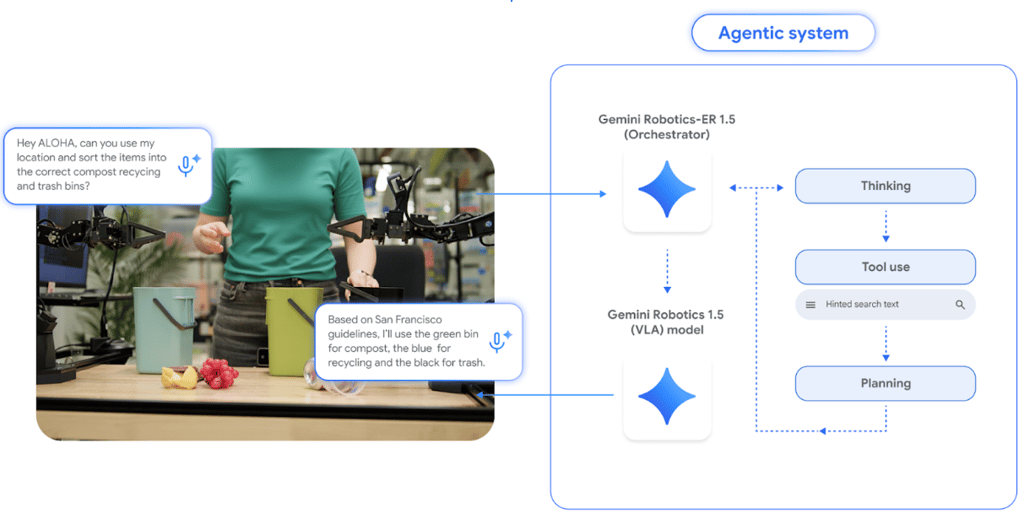
Robots That Reason: Google’s Gemini 1.5 Raises the Bar
Google has introduced Gemini Robotics 1.5 and Gemini Robotics-ER 1.5, new AI models built to power […]

How to restructure your security program to modernize defense
In 2024, Marriott received a harsh wake-up call: a federal order to restructure its security program. […]
Compliance Turns Digital Finance into Confidence
Compliance is not a regulatory imperative anymore, neither is it a strategic, confidence, strength, and growth […]

KI-Gefahren rücken Integritätsschutz in den Mittelpunkt
Data Poisoning gefährdet die Integrität von KI-Modellen. pixadot.studio – shutterstock.com Für CISOs reduziert KI selten die […]
