
The hard part of purple teaming starts after detection
In my recent articles for CSO, I’ve talked about the limits of current SOC models and […]

CISOs must separate signal from noise as CVE volume soars
In 2026, the cybersecurity industry is expected to cross a threshold it has never reached before: […]

Vorgetäuschte PDFs bergen neue Gefahren
loading=”lazy” width=”400px”>Cyberkriminelle verschicken ihre Malware als PDF-Dateien getarnt. IDG Der Security-Anbieter Malwarebytes hat kürzlich vor einer […]

Der Kaufratgeber für Breach & Attack Simulation Tools
Breach & Attack Simulation Tools geben Aufschluss darüber, wie gut (oder schlecht) Ihre Sicherheitskontrollen funktionieren. Roman […]

February 2026 Patch Tuesday: Six new and actively exploited Microsoft vulnerabilities addressed
Microsoft highlighted six new and actively exploited vulnerabilities among the 60 fixes issued in today’s February […]

BeyondTrust fixes critical RCE flaw in remote access tools
Companies using self-hosted versions of BeyondTrust Remote Support (RS) or Privileged Remote Access (PRA) should deploy […]
How to Prevent Active Directory Attacks by Securing Privileged Accounts
Key Takeaways Most Active Directory attacks succeed by abusing privileged accounts. Domain Admins are high-value targets […]

SolarWinds WHD zero-days from January are under attack
SolarWinds Web Help Desk (WHD) is under attack, with recent incidents exploiting a chain of zero-day […]

Your Office, Your Rules: Top Work-From-Home Career Ideas
Remember the days when “working from home” was a rare luxury or something only associated with […]
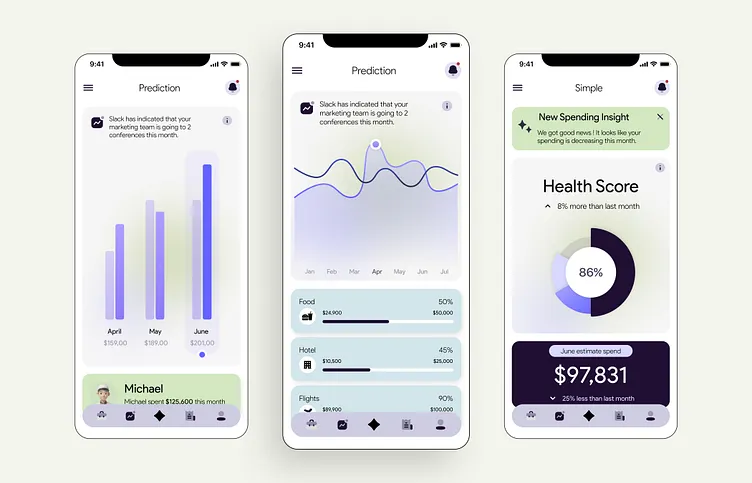
The Best Budget Tracking Apps for Financial Freedom
We’ve all been there. It’s a week before payday, and you glance at your bank account […]
