
Rogues gallery: 15 worst ransomware groups active today
Ransomware-as-a-service (RaaS) models, double extortion tactics, and increasing adoption of AI characterize the evolving ransomware threat […]

4 ways to prepare your SOC for agentic AI
a way to automate alert triage, threat investigation and eventually higher-level functions. According to IDC, agentic […]

PQC roadmap remains hazy as vendors race for early advantage
Post-quantum cryptography (PQC) has long sat on the periphery of enterprise security, with experts calling it […]

Tarnung als Taktik: Warum Ransomware-Angriffe raffinierter werden
Statt eines kurzen, aber sehr schmerzhaften Stiches setzen Cyberkrimelle zunehmend darauf, sich in ihren Opfern festzubeißen […]
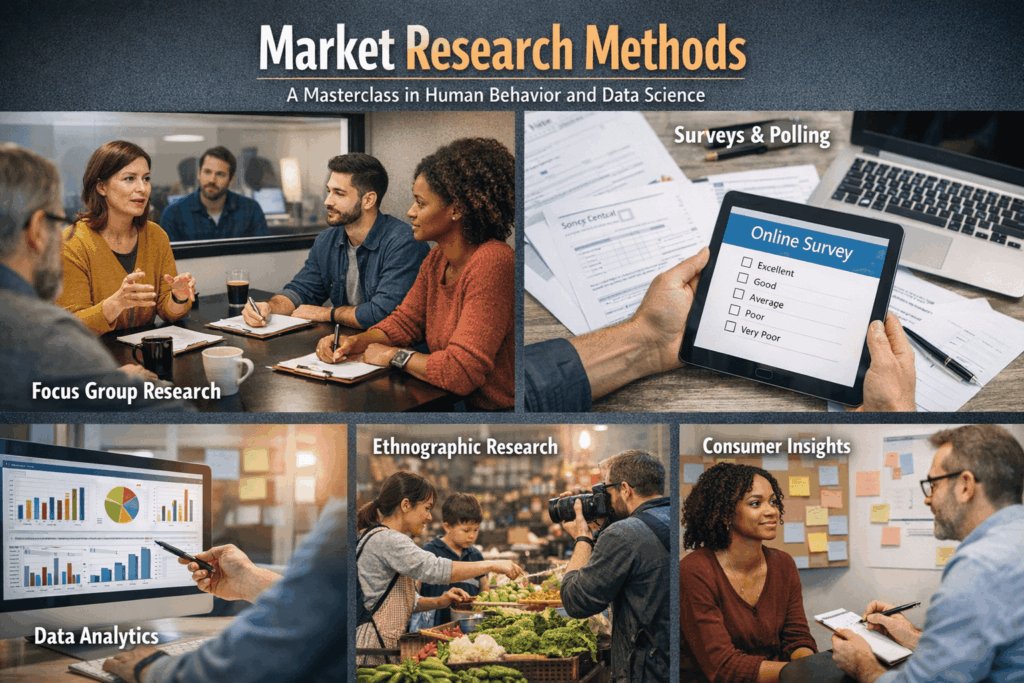
7 Proven Market Research Methods: The Masterclass in Human Behavior
Market research methods are the navigational charts of the business world; without them, you aren’t just […]

Trump’s cyber strategy emphasizes offensive operations, deregulation, AI
The White House released President Donald Trump’s long-awaited cybersecurity strategy, a lean seven-page blueprint that breaks […]

ClickFix attackers using new tactic to evade detection, says Microsoft
Threat actors are trying a different tactic to sucker employees into falling for ClickFix phishing attacks […]

Only 30 minutes per quarter on cyber risk: Why CISO-board conversations are falling short
Cybersecurity is, as it should be in this era of AI-driven cyberattacks, a regular item on […]

FBI wiretap system tapped by hackers
The US Federal Bureau of Investigation (FBI) has identified a suspected incident on a network used […]

OAuth vulnerability in n8n automation platform could lead to system compromise
A weakness in the configuration of OAuth credentials opens up a stored XSS vulnerability in the […]
