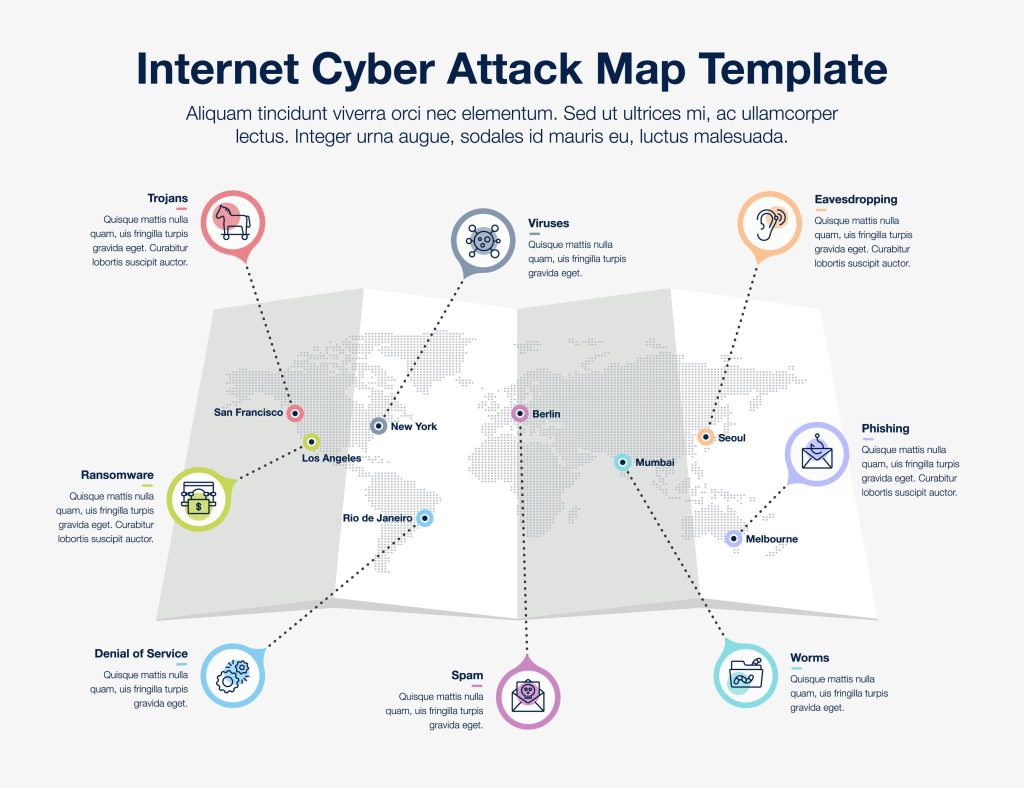
Shocking 12 Recent Major Cyber Attacks 2026 That Are Reshaping Global Security
The year 2026 has already witnessed an alarming rise in cybercrime activity worldwide. From large-scale ransomware […]
From DevOps to Runtime: Engineering the Right CWPP Strategy for Your Cloud Environment
Cloud-native architectures have fundamentally changed how organizations build, deploy, and scale applications. But they have also […]
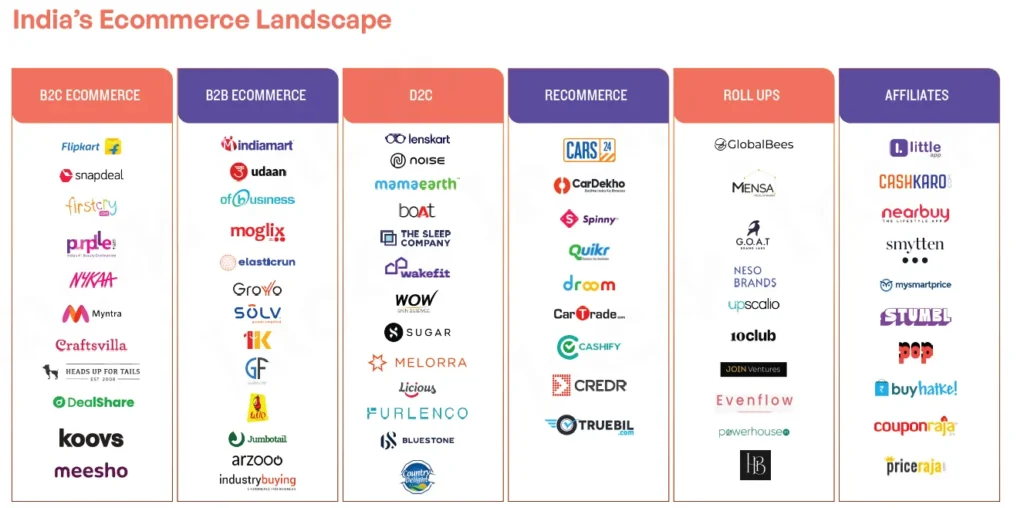
Best E-commerce Platforms for Selling Products Globally from India in 2026 🌍📦
Have you ever looked at a beautiful piece of handcrafted jewelry from Jaipur, a stack of […]
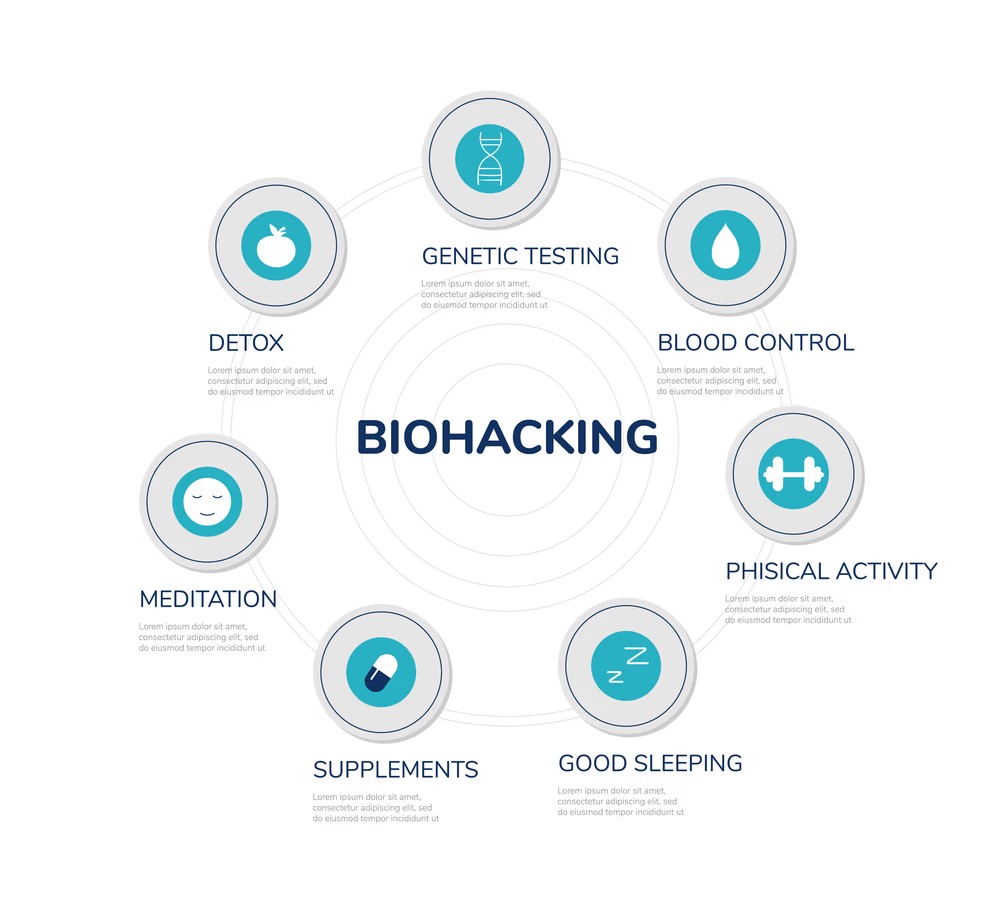
Biohacking for Beginners: 10 Simple Science-Backed Habits for Longevity 🧬✨
We’ve all seen those headlines about tech billionaires spending millions of dollars a year to “reverse” […]

AI for Freelancers: Smart Strategies to Double Your Income This Year 🚀
The freelance world is no longer about who can grind out the most hours; it’s about […]
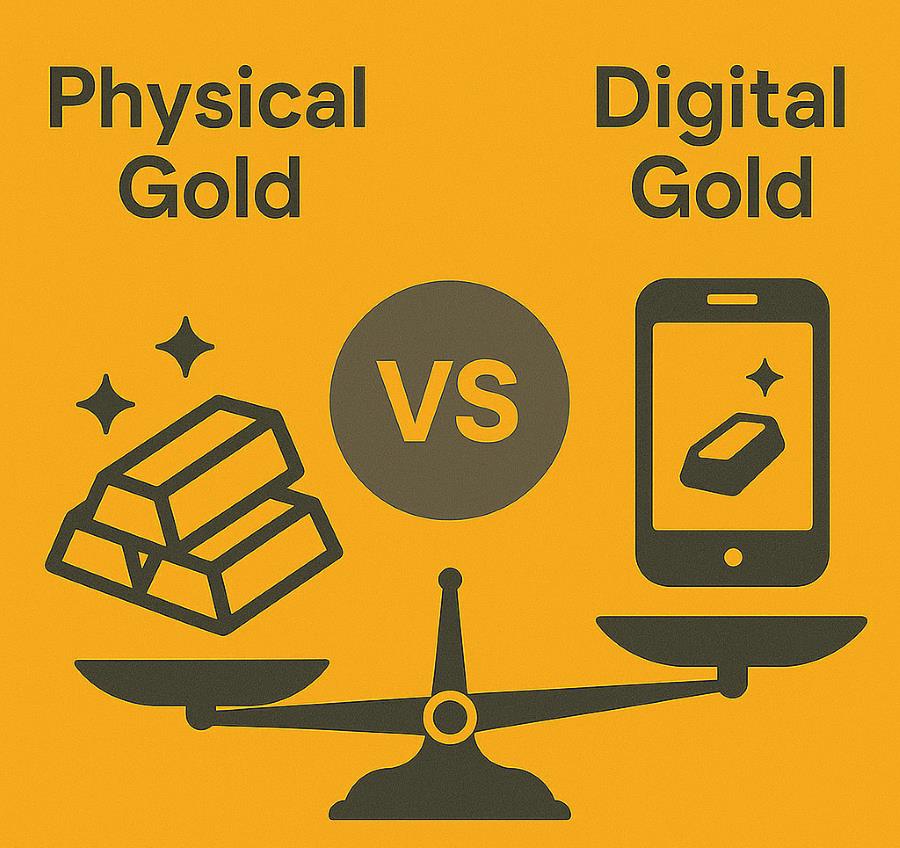
Physical Gold vs. Digital Gold: Which is the Better Investment in 2026? 🪙✨
If you’ve checked the news lately, you’ve probably noticed that gold is having a “moment” that […]

Seeing is Believing: How to Master Visual Search SEO with Google Lens 🔍
Remember the good old days of typing your exact query into a search bar? “Best Italian […]

Millionen Chrome-Erweiterungen geben Browserverlauf preis
width=”2489″ height=”1400″ sizes=”auto, (max-width: 2489px) 100vw, 2489px”>Eine Sicherheitslücke in beliebten Chrome-Erweiterungen führt dazu, dass der Browserverlauf […]

Flaws in four popular VS Code extensions left 128 million installs open to attack
Critical and high-severity vulnerabilities were found in four widely used Visual Studio Code extensions with a […]

Keenadu: Android malware that comes preinstalled and can’t be removed by users
There’s too little a user can do when hit with a complex Android malware that comes […]
