Best Practices for Integrating XDR into Your Security Stack
Key Takeaways XDR integration best practices turn fragmented tools into a coordinated, intelligence-driven security stack. Mapping […]
How Do CNAPP Platforms Help Prevent Misconfigurations Across Multi-Cloud Environments?
Key Takeaways CNAPP consolidates CSPM and CWPP into unified dashboards across AWS, Azure, GCP Effective CNAPPs […]
Email Organization: 7 Best Practices for a Productive Inbox
Email organization is the primary psychological barrier between professional flow and digital burnout. In an environment […]

10 Critical Lessons on the Emergency Fund Purpose: Your Financial Safety Net
Emergency fund purpose is the strategic decoupling of your daily survival from your immediate monthly income. […]

Web3 Simplified: Practical Everyday Uses of Blockchain Technology 🚀
Practical everyday uses of blockchain technology are no longer a futuristic dream; they are actively reshaping […]
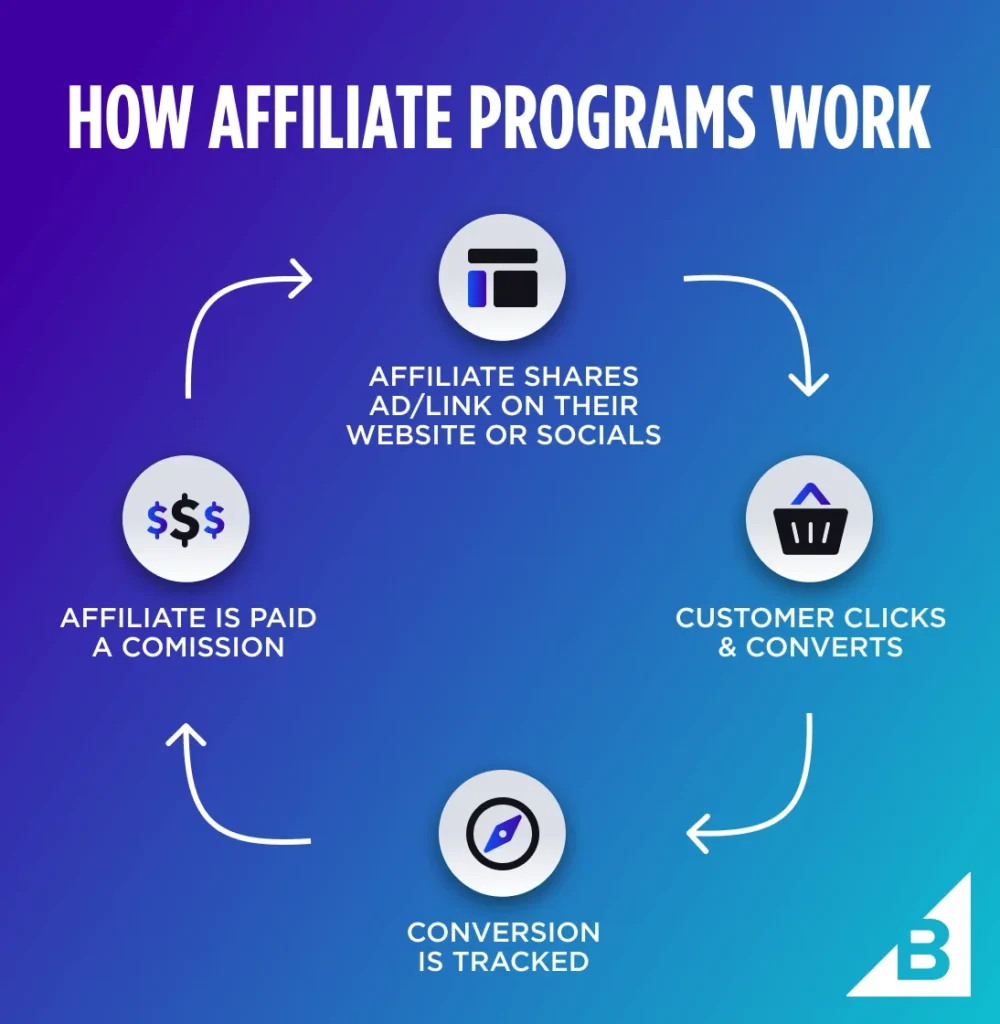
Best Affiliate Marketing Networks for New Bloggers and Creators 💸🚀
So, you’ve started a blog or a social media channel, and you’re consistently putting out content […]

Sleep Hygiene 101: The Best Gadgets and Evening Rituals for Deep Rest 🌙✨
We’ve all been there. You’ve had a long, productive day, your eyes are heavy, and all […]
Hello world!
Welcome to WordPress. This is your first post. Edit or delete it, then start writing!
Top 10 Soft Skills Every Tech Professional Needs to Survive 🚀👨💻
In the high-speed world of technology, your ability to write clean code, architect robust systems, or […]
Passive Income with REITs: A Complete Guide for Indian Investors 🏠💰
Real estate has always been the “crown jewel” of Indian households. Whether it’s the dream of […]