OpenAI Unveils ChatGPT Pulse to Deliver Personalised Daily Updates
ChatGPT can now search through your apps and chat history independently to generate personalised updates. These […]
Al Gore Launches AI Tool to Track 660 Million Global Air Polluters
Former Vice President Al Gore’s nonprofit coalition Climate TRACE has launched an artificial intelligence platform that […]
Performance Tax and Accounting Pros Can Count On (• Enterprise • AI News • eWeek)
Generic solutions and generic support just don’t cut it when tax deadlines and IRS compliance are […]
Microsoft AI CEO on the Danger of Considering AI Conscious: ‘There is Nothing Inside’
One of the recurring themes in conversations about generative AI is its ability to mimic human […]
Alibaba’s ‘Most Powerful’ AI Model: Qwen3-Max Packs 1 Trillion Parameters
Alibaba has released its most powerful AI model yet, the Qwen3-Max, a system with more than […]
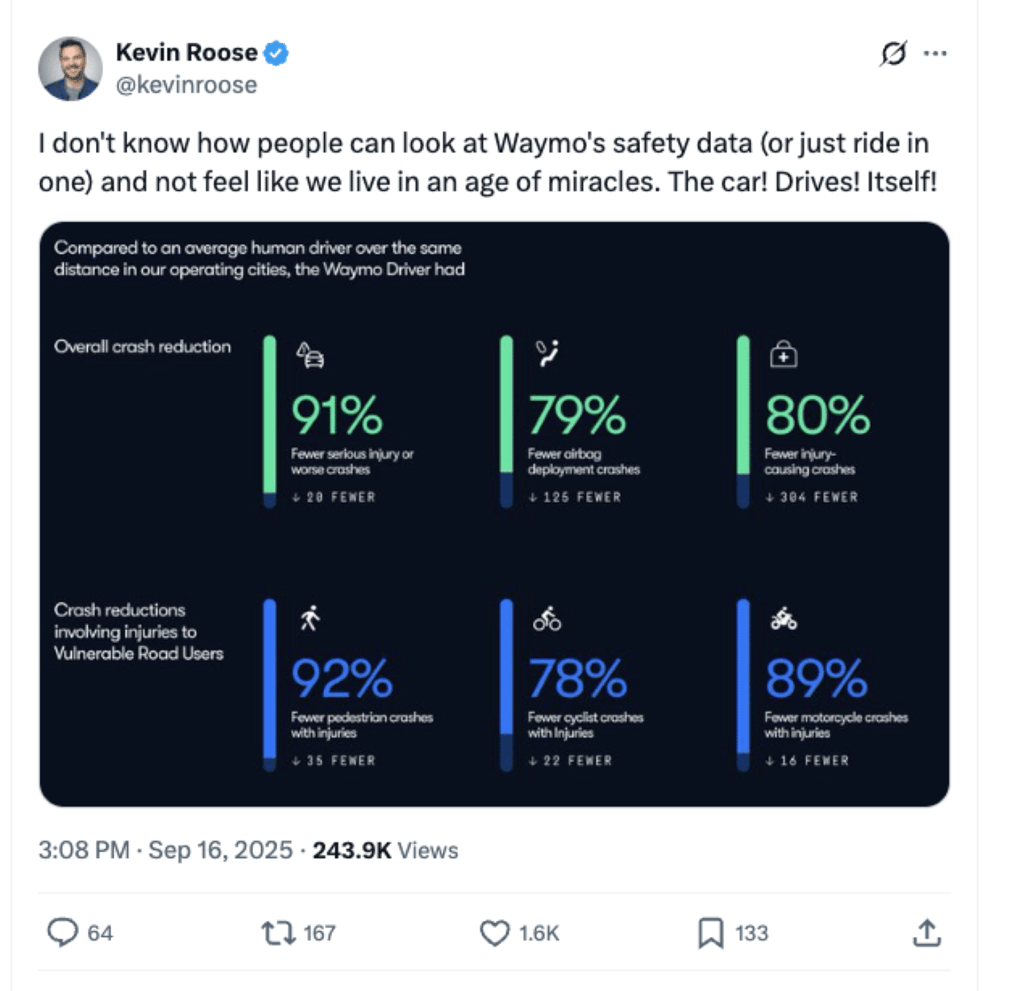
Waymo’s Safety Stats Are So Good, Even the Skeptics Are Running Out of Arguments
It’s been about a year since we last covered Alphabet’s driverless car company Waymo. Since then, […]
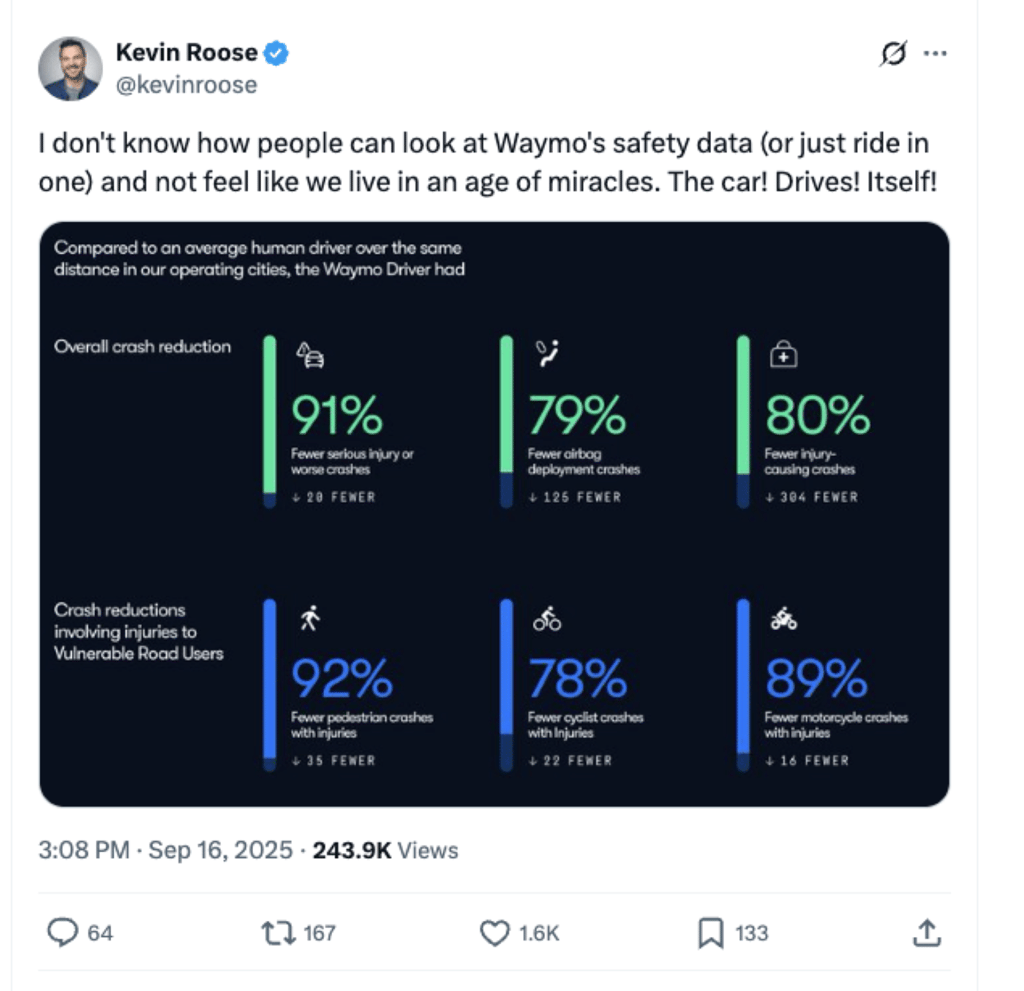
Waymo’s Safety Stats Are So Good, Even the Skeptics Are Running Out of Arguments
It’s been about a year since we last covered Alphabet’s driverless car company Waymo. Since then, […]
California Court Issues $10,000 ‘Warning’ Over Lawyer’s ChatGPT Brief
A California appeals court has fined Los Angeles attorney Amir Mostafavi $10,000 after he filed a […]
Turning Cloud Security Best Practices into Action with XDR
What once seemed like an optional upgrade has now become mission-critical: cloud security sits at the […]
Microsoft to Launch Marketplace for Publishers to Sell Content to AI Companies
Microsoft is planning to launch a marketplace that will allow publishers to sell their content to […]