
From Chaos to Calm: The Ultimate Guide to Home Organization in 2026 🏠✨
We’ve all been there. You walk through the front door after a long day, hoping for […]

Revolutionize Your Retail Therapy: The Best Shopping Apps of 2026 🛍️
Let’s be honest: the way we shop has changed forever. Remember the days of driving to […]

Scale Your Store to the Moon: The Best Dropshipping Tools for 2026 🚀
If you’ve spent any time in the world of e-commerce lately, you know that dropshipping is […]

Turn Your Phone into a Money Magnet: The Best Passive Income Apps for 2026 💸
Let’s be real for a second—everyone loves the idea of making money while they sleep. We’ve […]

Unleash Your Brand’s Visual Power: The Best AI Logo Generators of Today 🚀
In the fast-evolving digital landscape of 2026, a brand’s visual identity is its digital handshake. It’s […]
How Cloud-Native Applications Defend Against DDoS Attacks
Key Takeaways Cloud DDoS attacks are increasingly sophisticated, targeting APIs, microservices, and cloud workloads rather than […]
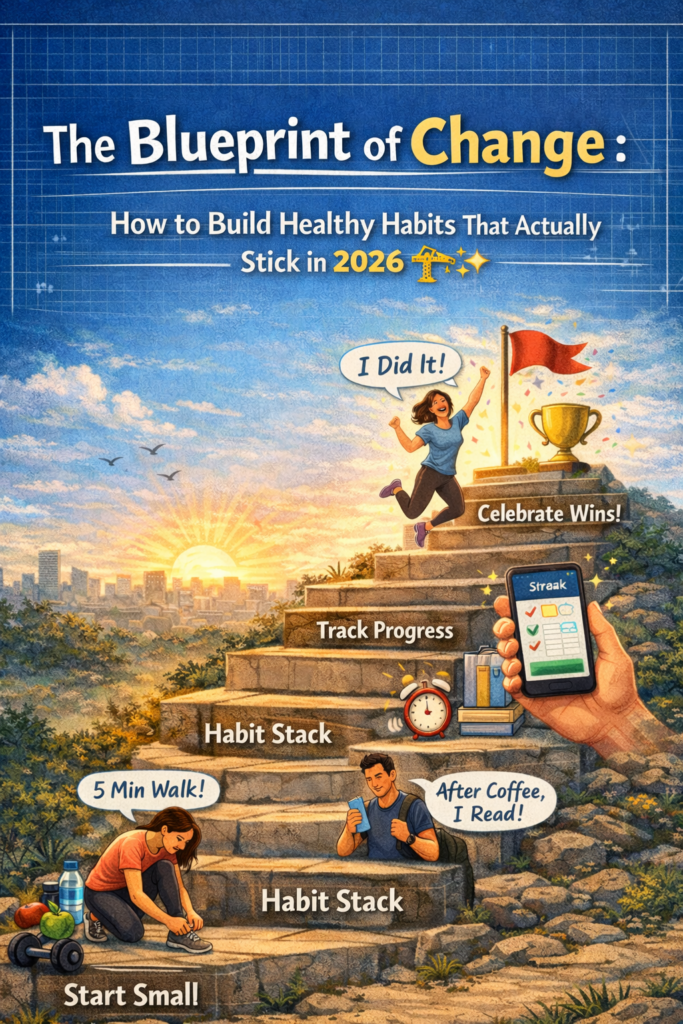
The Blueprint of Change: How to Build Healthy Habits That Actually Stick in 2026 🏗️✨
We’ve all been there. It’s January 1st (or a random Monday morning), and you are fired […]
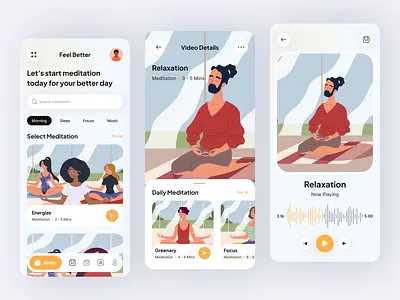
Finding Your Zen: The Best Meditation Apps to Quiet the Noise in 2026 🧘♂️✨
In a world that seems to be moving at 100 miles per hour, finding a moment […]
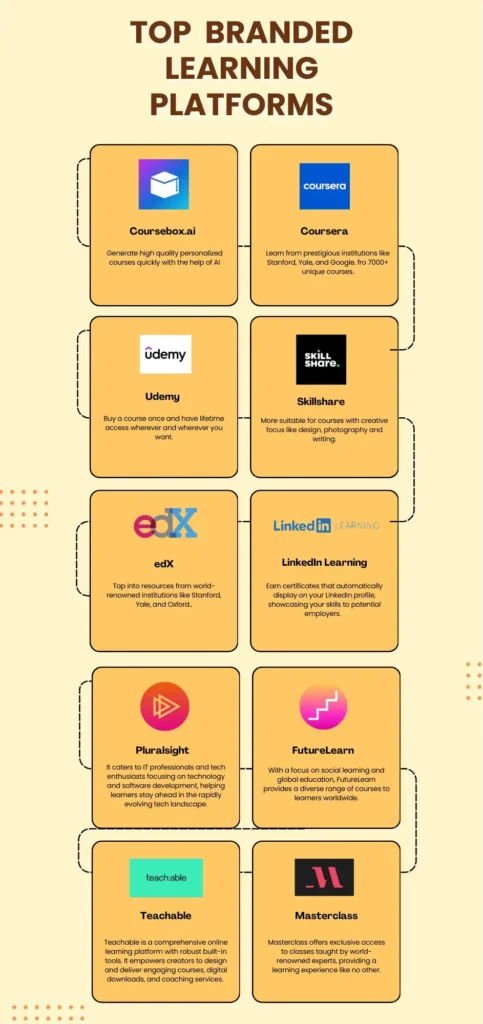
The Knowledge Gold Rush: Best Online Course Platforms for 2026 🎓✨
In 2026, the walls of the traditional classroom haven’t just crumbled—they’ve gone completely digital. We are […]

The Digital Safe: Best Crypto Wallets for Your Assets in 2026 🔐🚀
So, you’ve finally decided to join the decentralized revolution, or maybe you’re a seasoned “HODLer” looking […]