
Building Malware with Python: Writing Ransomware, Keyloggers & Reverse Shells from Scratch
Hey guys, Rocky here! 👋 So you’re curious how malware actually works? Maybe you’re wondering why […]

Building Malware with Python: Writing Ransomware, Keyloggers & Reverse Shells from Scratch
Hey guys, Rocky here! 👋 So you’re curious how malware actually works? Maybe you’re wondering why […]

Ransomware goes postal: US healthcare firms receive fake extortion letters
In late February, healthcare organizations across the US started receiving extortion demands by mail claiming that […]

Polnische Raumfahrtbehörde kämpft mit Cyberattacke
Die polnische Raumfahrtbehörde POLSA wurde Ziel eines Cyberangriffs. BUTENKOV ALEKSEI – Shutterstock.com Wie die polnische Raumfahrtbehörde […]

So werden PV-Anlagen digital angegriffen und geschützt
Unternehmen setzen vermehrt auf Solaranlagen mit Batteriespeichern, um hohe Energiekosten und Netzstabilitätsrisiken zu minimieren. Diese Systeme […]
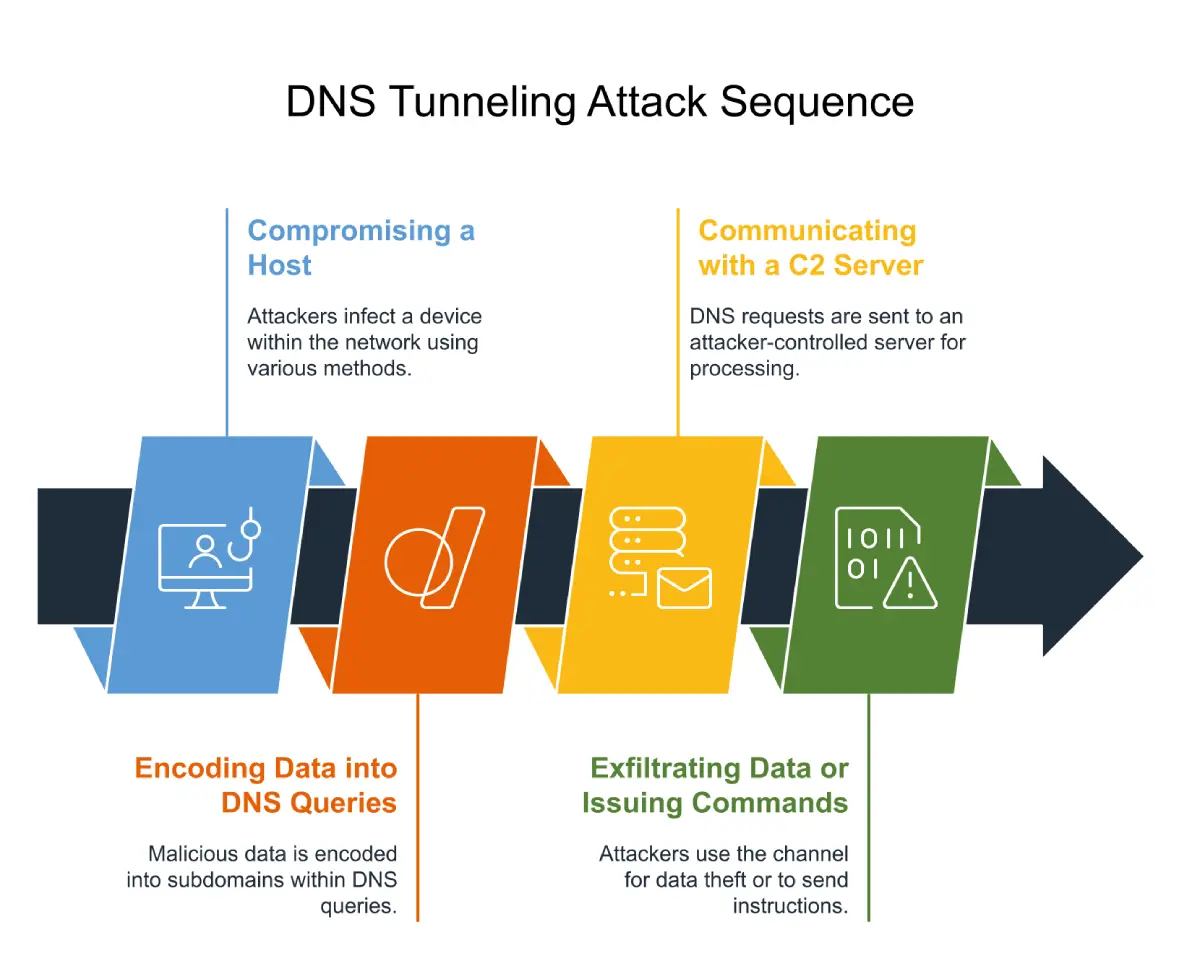
Detecting and Controlling Hidden DNS Tunnel Attacks
DNS is the backbone of the internet, translating domain names into IP addresses to facilitate communication […]
Tracking the Cybercriminal with Digital Forensics methodology
What is Digital Forensics Methodology? Digital forensics methodology is a scientific approach that uncovers and interprets […]

Critical vulnerabilities expose network security risks in Keysight’s infrastructure
Keysight Technologies’ Ixia Vision product family has been found to contain critical security vulnerabilities that could […]

The dirty dozen: 12 worst ransomware groups active today
Ransomware-as-a-service (RaaS) models, double extortion tactics, and increasing adoption of AI characterize the evolving ransomware threat […]

Chinese cyber espionage growing across all industry sectors
Security researchers are warning of a significant global rise in Chinese cyberespionage activity against organizations in […]
