
Zero-day exploits hit enterprises faster and harder
Google tracked 90 vulnerabilities exploited as zero-days last year, with Chinese cyberespionage groups doubling their count […]

Europa im Visier von Cyber-Identitätsdieben
Deutsche Unternehmen müssen sich warm anziehen: Sowohl staatliche als auch „private“ Akteure haben es auf sie […]

7 Anzeichen für akuten MSSP-Bedarf
Managed Security Service Provider können das Sicherheitsniveau nachhaltig steigern. Godlikeart | shutterstock.com Ein Managed Security Service […]

LeakBase marketplace unplugged by cops in 14 countries
The LeakBase cyberforum, considered one of the world’s largest online marketplaces for cybercriminals to buy and […]

How Does Endpoint Deception Detect Attacks Before Damage Happens?
Key Takeaways Endpoint deception technology helps detect threats before exploitation spreads. Deception endpoint coverage expands visibility […]
Detecting Living-off-the-Land Attacks in OT Networks
Key Takeaways LOTL attacks use trusted tools like PowerShell, WMI, and RDP, making malicious activity appear […]

Cisco issues emergency patches for critical firewall vulnerabilities
Cisco has handed security teams one of the largest ever patching workloads affecting its firewall products, […]

Coruna iOS exploit kit moved from spy tool to mass criminal campaign in under a year
Google’s threat intelligence researchers have identified a sophisticated exploit kit targeting iPhones that was first used […]

Europol: Großer Markt für gestohlene Daten geschlossen
Europol koordinierte den Schlag gegen Leakbase. PixelBiss – shutterstock.com Die Polizei von Amsterdam hat im Zuge […]
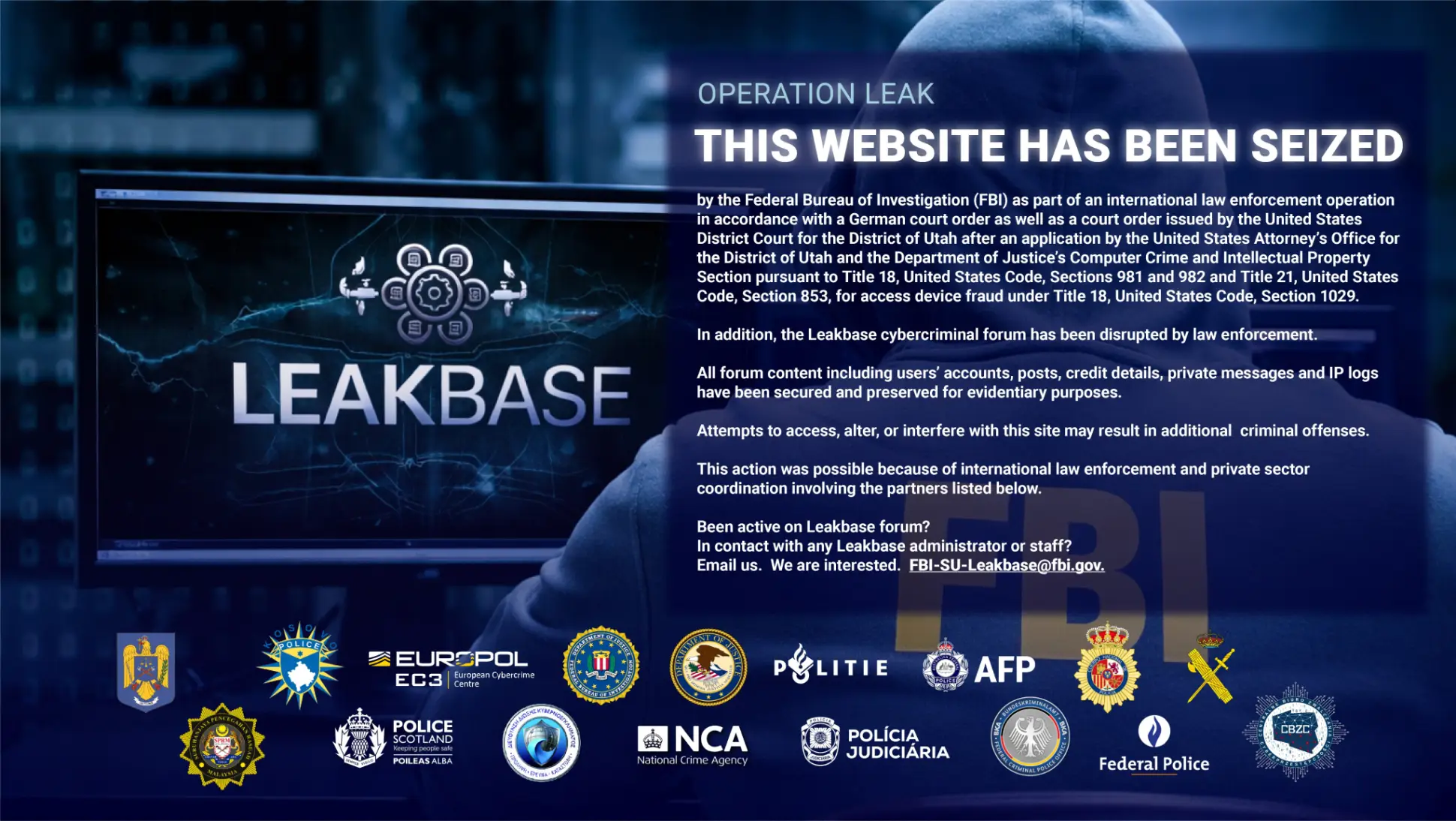
Europol schließt riesigen Markt für gestohlene Daten
loading=”lazy” width=”400px”>LeakBase wird von den Strafverfolgungsbehörden untersucht. Die Polizei von Amsterdam hat im Zuge einer internationalen […]
